Hidden Secrets: Ritualistic Sexual Abuse & Mind Control
- A. Royden D'Souza

- Mar 30
- 92 min read
In September 2025, a Netflix limited series appeared and quietly became the streamer's No. 1 global television show. It was called Wayward, created by and starring the Canadian comedian Mae Martin, and it told a story that was, on its surface, about a sinister school for "troubled teens" in a picture-perfect Vermont town.
But beneath that surface, Wayward did something remarkable: it laid out, in narrative form, the architecture of a system that most of the world has been told never existed.

The series follows two parallel narratives. In one, two teenage best friends, Abbie and Leila, are separated when Abbie is sent to Tall Pines Academy, a facility run by the enigmatic and terrifying Evelyn Wade (Toni Collette).
There, they discover a brutal hierarchy of "phases"—Burrow, Break, Build, Ascend—that culminates in a mysterious ceremony called "the Leap," which promises to free the students from their trauma but actually subjects them to drug-induced psychological torture designed to break down their identities and rebuild them as obedient followers.
In the other narrative, a police officer named Alex (Martin) and his pregnant wife Laura (Sarah Gadon) move to Tall Pines, only to discover that Laura is a former student of Evelyn's, that the entire town is populated by Evelyn's "graduates," and that the system they are confronting is not a single abusive institution but a multigenerational network of control.
Wayward does not mention MK-Ultra. It does not mention Satanic Ritual Abuse (SRA) or Ritualistic Sexual Abuse (RSA). It does not mention the CIA, or Operation Paperclip, or the recruitment of war criminals. But its narrative structure is a near-perfect map of the stages of trauma-based mind control that survivors, whistleblowers, and investigative journalists have been documenting for decades.
The "phases" at Tall Pines correspond directly to the stages of programming described in survivor testimony. Evelyn's methods mirror the techniques allegedly leveraged by the CIA. And the series' ambiguous ending in which Laura, the victim, becomes the new cult leader illuminates the most disturbing truth about these systems: they reproduce themselves across generations, turning the abused into the abusers.
This paper uses Wayward as a narrative framework to examine the broader phenomenon of trauma‑based mind control; specifically its manifestations as Satanic Ritual Abuse (SRA) and Ritualistic Sexual Abuse (RSA). We will trace the history from its ancient roots through its systematization in the 20th century, analyze the documented evidence for government programs like MK‑Ultra, examine the moral panic that simultaneously revealed and obscured the truth, and apply cold, pattern‑based logic to separate what can be proven from what remains contested.
The central thesis is that trauma-based mind control is a documented historical reality, but that the phenomenon has been deliberately obscured by a combination of institutional cover-up, legitimate scientific skepticism, and the conflation of verified abuse with the moral panic that erupted in the 1980s.
Wayward serves as a Rosetta Stone, a fictional account that, precisely because it is fiction, can show us the architecture of a truth that has been systematically buried.
Part I: The Deep Roots of Ritualistic Sexual Abuse
Before examining the specific manifestations of trauma-based mind control, it is essential to understand its historical antecedents. Throughout human history, societies have used ritualized trauma to break individuals and reshape them. The mechanisms may have evolved, but the architecture remains remarkably consistent.
In Wayward, the first phase of Evelyn's program is called "Burrow." New students are stripped of their identities, isolated from the outside world, and forced to confront the foundations of their supposed "brokenness."
They are given gray jumpsuits, assigned to sterile dormitories, and subjected to a regime of deprivation and surveillance. The goal is not healing but disorientation: to cut the students off from everything they knew so that they can be rebuilt in Evelyn's image.
This phase mirrors the historical reality of how mind control systems have always operated. Before the mind can be programmed, it must be isolated. Before a new identity can be implanted, the old identity must be stripped away.

Defining the Terms: SRA, RSA, and MK-Ultra
Before proceeding, it is essential to distinguish between the three forms of trauma-based mind control that this paper will analyze.
Satanic Ritual Abuse (SRA): It refers to abuse committed in a ritualistic context that explicitly invokes Satanic or occult symbolism. Survivors describe ceremonies involving inverted crosses, black robes, ritual sacrifice of animals (or, in extreme allegations, human infants), and the use of Satanic iconography to induce terror and dissociation. The symbolism is meant to instill a sense of cosmic evil, that the abuser commands supernatural forces, making the victim feel that escape is impossible.
Ritualistic Sexual Abuse (RSA): It is a broader category that encompasses abuse conducted within any organized, ritualized setting, whether religious, political, or pseudo-therapeutic, that may or may not involve Satanic trappings. RSA can occur in cults, intelligence-linked networks, child trafficking rings, or even "therapeutic" programs like the troubled-teen industry depicted in Wayward. The rituals may include elaborate ceremonies, the use of costumes or uniforms, forced drug ingestion, filmed abuse, and staged "rebirth" or "initiation" rites.
MK-Ultra: It was the CIA's official mind control program, operational from 1953 to the early 1960s. It represented the most extensive government effort to develop mind control techniques in American history, involving LSD, electroshock, sensory deprivation, and torture on unwitting subjects. The program's records were deliberately destroyed in 1973, and its full scope may never be known.
Despite their different contexts—hereditary cults (SRA), organized trafficking networks (RSA), and state intelligence programs (MK-Ultra)—these three phenomena share the same underlying architecture. They all rely on the systematic application of the five-phase process that Wayward dramatizes: Burrow, Break, Build, Ascend, Leap.

Part II: The Five Phases of Trauma-Based Mind Control
Before analyzing each phase in detail, it is crucial to understand what programming actually is; and what it is not. The terms "mind control" and "programming" conjure images of sci-fi gadgets, Manchurian Candidate brainwashing machines, or magic potions.
That is probably by design. The very words have been weaponized to make the phenomenon seem implausible; something only conspiracy theorists believe in.

But in reality, programming is just the deliberate use of ordinary human psychology. Every human being is already programmed. From infancy, we learn language, social norms, trauma responses, and identity through repetition, reward, punishment, and attachment. This is not magic; it is how brains work.
What trauma-based mind control does is hijack that natural process. It breaks down the existing programming (through isolation, pain, fear) and installs new patterns—dissociative identities, amnesiac barriers, conditioned triggers—using the same mechanisms of repetition, reward, and terror. The result is not a robot, but a person whose psyche has been fractured and rearranged by the abuser.
There are no mind-control rays or magic potions. There is only the systematic application of what we already know: that the human mind is shaped by experience. The cruelty is not in the mechanism; it is in the deliberate, calculated destruction and reconstruction of a victim's mind.
As the NIH paper on appeasement explains, when faced with life-threatening situations, the nervous system reverts to foundational survival circuits that supplant intentional behavior. Dissociation serves as a protective buffer, allowing tolerance of the intolerable. This neurobiological reality is what abusers exploit.
Imagine a child cornered by an adult who has been both their protector and their tormentor. The adult’s face is twisted in rage; there is nowhere to run, no one to call. The child’s nervous system, recognizing that fight or flight will only bring more pain, makes a split‑second, ancient calculation: freeze. The heart slows. The mind drifts; walls soften, sound becomes distant. The child is still there, but not there.
This is a classic description of dissociation; specifically the forms known as depersonalization (feeling detached from oneself, as if watching from outside) and derealization (the world becoming unreal, distant, muffled). In trauma psychology, dissociation is understood as an involuntary survival response: when the threat is inescapable, the mind "leaves" the body to reduce the immediate pain and terror. That "still there, but not there" sensation is the hallmark of the dissociative state.
When the adult later brings them a treat and speaks gently, the child’s body remembers that compliance made the danger stop. That is not weakness or choice. It is the neurobiology of survival, hijacked and weaponized. This is what abusers—whether a cult leader, a CIA interrogator, or a domestic partner—learn to exploit: the moment the nervous system surrenders to save itself.
So when you read "programming" or "mind control," do not imagine fiction. Imagine the victim being taught, through unbearable pain, that certain sounds, symbols, or touches will trigger a switch in their own mind; a switch they did not choose and cannot explain. That is not fantasy. It is the dark side of how learning works.
Phase 1: Burrow — Isolation and Identity Stripping
The first phase of any programming system is isolation. The victim must be cut off from everything that defines their existing identity: family, friends, familiar environments, sources of safety and comfort.
This phase is called "Burrow" in Wayward because the victim is buried; removed from the world, placed in a controlled environment where every aspect of existence is monitored and manipulated.

SRA (Hereditary/Intergenerational Cults)
In hereditary SRA systems, the Burrow phase begins at birth; sometimes before. The child is born into a closed community that has already isolated itself from the outside world.
Multi-generational cults often operate on remote compounds, in isolated rural areas, or within closed ethnic or religious communities. The child never experiences an outside identity to be stripped away; the isolation is total from the start.
The Burrow phase in SRA also operates through "grooming": the gradual process of gaining trust, establishing authority, and normalizing abuse. An elder in the cult may present themselves as a caregiver, a mentor, a spiritual guide.
They "burrow" into the child's life by becoming the source of both comfort and terror. The child learns that this person controls everything—food, shelter, safety, love—and that defiance means pain.
In survivor testimony documented by Alison Miller, one victim described how her grandmother—the cult's high priestess—began grooming her at age three: "She would tell me I was special, that I had been chosen. She would take me into her room and show me beautiful things. Then she would hurt me, and tell me that only she could protect me from the evil outside."
RSA (Organized Trafficking Networks)
In RSA networks, the Burrow phase often begins with recruitment; a process that can look indistinguishable from ordinary social interaction. A vulnerable young person, often from a broken home or unstable environment, is identified by a recruiter. They are offered friendship, protection, money, affection. They are slowly drawn into a web of dependency.
The recruiter "burrows" into the victim's life, becoming indispensable. They provide what the victim lacks: stability, attention, a sense of belonging. Only gradually is the victim introduced to the darker reality; that this relationship demands payment, that the network expects compliance, that leaving means losing everything they have been given.
The NIH paper on appeasement describes this dynamic: "Social connection to the perpetrator may be experienced as a type of lifeline" when basic survival needs are at stake. The abuser becomes, paradoxically, the victim's only source of safety; a psychological trap that makes escape nearly impossible.
MK-Ultra (State Intelligence Programs)
In MK-Ultra, the Burrow phase operated through selection and capture. The CIA did not have the luxury of multi-generational cult structures; they needed subjects they could control in a finite timeframe. Subjects were selected from vulnerable populations: prisoners, mental patients, the homeless, foreign nationals who could disappear without notice.
The Chinese state media investigation into MK-Ultra documents how children as young as 11 were recruited in Denmark: "They were paid 16 Danish kroner each to come do something fun. Then they were taken to a hospital, strapped to chairs, and subjected to electric shocks and piercing noise through headphones."
The Burrow phase in MK-Ultra was clinical rather than familial. The subject was removed from their environment, placed in a controlled facility, stripped of their belongings, their clothing, their name. They were assigned numbers. They were isolated in sensory deprivation chambers. They were cut off from any external contact.
Sidney Gottlieb, the chemist who ran MK-Ultra, called this the "blast away the existing mind" phase. Before you could implant a new mind, you had to ensure the old mind had nothing left to hold onto. What SRA and RSA took over a decade to accomplish, they wanted to complete the process in a few months/years.
Phase 2: Break — The Shattering of Identity
The second phase is the core of the programming process. Having isolated the victim, the abuser now subjects them to trauma so intense, so systematic, that the existing personality fractures. The mind dissociates to survive. Multiple identities—"alters"—form to contain different aspects of the experience.
In Wayward, this is the "Break" phase. Students are subjected to the "Electric Chair" (the "Hot Seat"), where they are forced to sit in a circle and hurl criticisms at one another while staff members observe and intervene. They are locked in the "Mirror Room," where they are forced to confront their own reflections in psychological torture. They are deprived of food, sleep, and human connection.

SRA: Demonic Rituals, Torture, and Forced Witnessing
In SRA systems, the Break phase is often staged as ritual. The child is taken to a ceremony, perhaps a basement, perhaps a remote location, where they witness or are forced to participate in acts designed to shatter their sense of reality.
Survivor testimony describes:
Forced witnessing of animal or human sacrifice
Sexual abuse by multiple perpetrators, often in costume or mask
Being buried alive or placed in coffins to simulate death
Forced ingestion of blood, flesh, or drugs
Being made to participate in the abuse of other children
The ritual elements serve a specific psychological function. By invoking Satanic or occult symbolism, the abuser makes the trauma cosmic in scale.
The child is not merely being hurt by a person; they are being hurt by forces of ultimate evil. Resistance becomes not just futile but cosmically meaningless. The dissociation that follows is not a choice but a survival imperative.
A survivor writing under the name Svali described how this worked in the cult she escaped: "After a long session of torture, the child is released... They will be given a small animal, often a kitten, and told to wring its neck. The child will refuse. The child will then be placed back in the cage, or hooked back up to the electrodes, and shocked again... Finally, shaking, they will do as they are ordered. Afterwards, they will often go into the corner and vomit, all the while being praised by their trainer for the 'good job' that they have done."
Alison Miller, a therapist specializing in ritual abuse survivors, documents that the Break phase in SRA is designed to create what she calls 'engineered personality systems': "The abusers deliberately create dissociative splits by timing trauma to specific cues. A child being shocked while a bell rings will associate the bell with pain, and may develop an alter that only emerges when that bell sounds."
RSA: Sexual Torture, Trafficking, and Filmed Abuse
In RSA networks, the Break phase centers on sexual torture and the creation of blackmail material. The victim is subjected to repeated, often ritualized sexual abuse; sometimes by multiple perpetrators, sometimes filmed, sometimes in settings designed to maximize degradation.
The RSA Break phase serves multiple functions:
Trauma bonding: The victim develops a dissociative attachment to the abuser, a survival mechanism now understood as appeasement rather than pathology
Blackmail creation: Filmed abuse becomes a tool of control; the victim knows that if they speak, the evidence will destroy them
Normalization of abuse: The victim learns that abuse is normal, that resistance is pointless, that their body is not their own
The NIH paper on appeasement explains the neurobiology of this process: "When faced with a life threat, the foundational survival circuits originating in the brainstem... move the nervous system into a defensive state that supplants intentional behavior and social interactions. Dissociation is an unconscious process that serves as a protective buffer when a threat is imminent." The victim is not 'bonding' with the abuser out of affection; they are appeasing a threat to survive.
MK-Ultra: Drug-Induced Ego Dissolution and Electroshock
In MK-Ultra, the Break phase was conducted with scientific precision. Subjects were administered massive doses of LSD, often for weeks or months at a time, to break down psychological defenses.
They were subjected to electroshock therapy not for therapeutic purposes but as a tool of disorientation. They were placed in sensory deprivation tanks to induce hallucination and dissociation.
The CIA's goal was what Gottlieb (fall-guy) called "blasting away the existing mind." They wanted to create a state of psychic blankness onto which a new identity could be written. Subjects in MK-Ultra experiments described losing all sense of self, all memory of who they had been, all ability to distinguish reality from hallucination.
One MK-Ultra subject, future Boston crime boss James "Whitey" Bulger, was given LSD every day for more than a year while incarcerated. He later wrote that he thought he was going insane, that the experiment had been a "greater crime" than any he had committed.
Phase 3: Build — Implanting the New Identity
Having broken down the victim's existing identity, the abuser now begins the process of building a new one. In Wayward, this is the "Build" phase: students are assigned to adoptive parents in the town, given new identities, and taught to suppress their memories of what happened to them.
The goal is not liberation but replacement: the old self is killed, and a new self, one that serves Evelyn's purposes, is constructed in its place.

SRA: Programming, Conditioning, and the Illusion of Love
In SRA systems, the Build phase involves the systematic implantation of programmed responses. The child is shown "the good side"—the family setting, the moments of apparent love and care that follow the trauma. The abuser alternates terror with affection, creating what survivors call "the cycle."
Survivors describe that after the torture sessions, the same abuser would hold them, feed them, give them gifts, and whisper: "I'm the only one who loves you. No one outside will understand. They will think you're evil. But I will always protect you."
The child, whose nervous system has been shattered, clings to this affection as the only respite from pain. Over years, this alternation creates what Alison Miller calls a "trauma bond" where love and terror become fused. The abuser becomes both the source of unbearable pain and the only source of safety; a psychological trap that can last a lifetime.
This is the Build phase: the abuser creates a split that obeys, to avoid the horrendous pain of disobedience. The child learns that the only way to receive love, or simply to stop the pain, is to become whatever the abuser demands.
The illusion of love is critical. After trauma, the abuser provides comfort. This creates what the NIH paper calls "appeasement": the victim learns to calm the perpetrator through submission, to seek safety through compliance. The abuser becomes both the source of terror and the only source of safety; a psychological trap that can last a lifetime.
RSA: Trauma Bonding and the Creation of Dependency
In RSA networks, the Build phase operates through what was once called Stockholm syndrome but is now more accurately understood as appeasement. The victim, having been broken, is now "rebuilt" as a compliant asset. They are given small privileges, moments of apparent normalcy, the illusion of choice.
The survivor's testimony about her grandmother's grooming illustrates this: "She would hurt me, and then she would hold me and tell me she was the only one who could keep me safe. She would tell me that outside, everyone would hate me, that I was dirty, that only she could love me."
The Build phase creates a dependency that mimics love. The victim may develop alters specifically designed to experience this "love," parts of the self that believe they are in a consensual relationship with the abuser, that believe they have chosen this life, that believe escape would be death.
MK-Ultra: The Failed Goal of Mind Control
The official narrative of MK-Ultra is that Gottlieb never succeeded in the Build phase. He could "blast away the existing mind," but he could not reliably "insert a new mind" into the resulting void. The program was considered a failure and shut down.
But survivors and researchers argue that this is not where the story ends. They contend that MK-Ultra did not disappear; it went underground, its methods passed from intelligence agencies to organized crime networks, cults, and the upper echelons of society.
The Build phase, they argue, was perfected not in CIA labs but in the secret programs that continued after the official termination.
Phase 4: Ascend — The Victim Prepared for Society Under Supervision
The fourth phase is when the victim is deemed ready to function in the outside world; but under the continued control of handlers or supervisors. In Wayward, this is the "Ascend" phase: students are released from the strict confinement of Tall Pines and placed in the surrounding town, where they live apparently normal lives while remaining under Evelyn's control.
The Ascend phase is critical because it makes the system self-sustaining. The victim does not need to be physically confined; they are confined by their programming. They may hold jobs, have relationships, raise families; all while remaining loyal to their abusers.

SRA: The "Sleeper" and the Double Life
In SRA systems, the Ascend phase involves the creation of what survivors call "sleepers"—programmed individuals who live ordinary lives but can be activated by triggers.
They may have careers, families, social standing. They may have no conscious memory of their programming. But specific cues, like a phrase, a symbol, or a touch can "switch them on," activating programmed alters.
One survivor described how her cult placed her in a professional career: "They trained me to be a therapist. I went to school, got my license, built a practice. And all the while, I had alters who would come out when I was triggered. I would treat patients, and sometimes I would dissociate and not remember whole sessions. My handler would call me and give me assignments. I didn't know what I was doing."
The Ascend phase serves multiple functions for the cult. Programmed individuals can:
Provide financial support
Recruit new members
Gather intelligence on outsiders
Provide "cover" as respected community members
Serve as sources of children for the next generation
RSA: The Trafficking Network and the "Normal" Life
In RSA networks, the Ascend phase often involves the victim being placed in a seemingly normal environment while remaining available to abusers. They may be placed in foster care, group homes, or adoptive families that are themselves part of the network. They may be given apartments, cars, money; all of which can be taken away if they disobey.
The Wayward depiction of Tall Pines as a town full of Evelyn's graduates captures this precisely. The victims are not locked away; they live in the community, run businesses, serve on the police force. They appear normal. But their freedom is an illusion. The town itself is the cage.
MK-Ultra: The "Asset" and the Intelligence Network
If MK-Ultra succeeded in the Build phase, a question that remains contested, then the Ascend phase would involve the placement of programmed individuals as intelligence assets. These "Manchurian Candidates" would be placed in positions of influence, activated/used only when needed, with or without memory of their programming.
There is no definitive proof that such individuals exist. But the pattern of intelligence operations suggests that the capability, if developed, would not have been abandoned. As the Chinese investigation into MK-Ultra notes, "the Americans are very good at hiding information. What happened after 1973 remains classified."
Phase 5: Leap — Complete Brainwashing and Transformation into Abuser
The final phase is the most disturbing. In Wayward, this is the "Leap," the drug-induced ceremony that is supposed to free students from their trauma but instead subjects them to psychological torture designed to erase their identities and rebuild them as obedient followers.
The series' ending reveals the ultimate horror: Laura, the victim, becomes the new Evelyn. The cycle continues. The abused becomes the abuser.

SRA: The Forced Perpetrator
In SRA systems, the Leap phase involves forcing the victim to become an abuser themselves. Children are made to participate in the abuse of other children. Teenagers are forced to lead rituals. Young adults are given their own victims to control.
Svali's testimony describes this progression: "By age 12, most children are very accurate with a small pistol or rifle... They are then taken to an enclosure, and taught to practice shooting animals... During virtual reality exercises, animal targets are replaced with human ones. The child is taught to hit the 'bad guys'... One day, they are told to shoot their parent or sibling, who is simulated graphically in the VR program. They do. At this point, the child is considered 'reliable' on 'command'."
The creation of forced perpetrators serves multiple functions:
It ensures silence: the victim is now complicit
It creates a permanent bond: the victim has crossed a line they can never uncross
It replicates the system: each generation of victims becomes the next generation of abusers
RSA: The Recruiter
In RSA networks, the Leap phase similarly involves turning the victim into a recruiter. Victims are taught to identify vulnerable individuals—often from their own communities, their own families—and to bring them into the network. They become the "friendly face" that new victims trust.
Laura's transformation in Wayward—from victim of Evelyn to the new leader of Tall Pines—captures this process precisely. She does not escape the system; she becomes its new custodian. Her rhetoric is softer, her methods gentler, but the underlying structure remains. The cycle of control continues, passed from generation to generation.
MK-Ultra: The Asset Becomes the Handler
If MK-Ultra successfully created programmed individuals, the Leap phase would involve those individuals being placed in positions where they could recruit and control others. The asset becomes the handler. The system perpetuates itself.
This is the ultimate horror of trauma-based mind control. It is not merely that individuals are broken; it is that the broken are turned into breakers. The system reproduces itself through its victims. And the line between victim and perpetrator becomes permanently blurred.
Part III: The Evidence for SRA and RSA
The most direct evidence for SRA and RSA comes from survivor testimony. Organizations like Survivorship and S.M.A.R.T. (Stop Mind-control And Ritual abuse Today) exist to support these individuals, and their conferences bring together survivors, therapists, and researchers who believe that such abuse is a real and ongoing phenomenon.

The survivor testimony is consistent across thousands of cases. Survivors describe:
Being abused from infancy, often by family members
Being subjected to electric shocks, sensory deprivation, and forced drug ingestion
Being forced to participate in rituals involving animal sacrifice, blood, and occult symbolism
Being programmed with multiple personalities that can be triggered by specific cues
Being made to abuse other children
Being threatened with death if they speak
Svali's testimony about assassin programming is among the most detailed. She describes a systematic process starting at age two, progressing through animal killing, weapons training, and finally simulated human killing; all designed to create a child who can kill on command.
Alison Miller's manual for therapists, Demystifying Mind Control and Ritual Abuse, provides clinical validation of these testimonies.
Miller, who has worked with survivors for decades, documents the specific programming structures she has encountered: engineered personality systems, programmed triggers, internal hierarchies of alters, and the use of ritual to create dissociative barriers.
The Moral Panic Thesis: What Skeptics Argue
The mainstream academic and legal consensus holds that SRA was a moral panic; a period of mass hysteria in the 1980s and 1990s in which false allegations of Satanic ritual abuse were spread by overzealous therapists, law enforcement officers, and religious fundamentalists.
The evidence for the moral panic thesis includes:
The absence of corroborating physical evidence in the vast majority of cases
The use of discredited therapeutic techniques, including hypnosis, guided imagery, and suggestive questioning, to "recover" memories
The involvement of therapists who explicitly believed in Satanic conspiracies
The collapse of major prosecutions, including the McMartin preschool trial, which lasted seven years and resulted in no convictions
The McMartin case is often cited as emblematic of the moral panic. Over a period of years, children at a California preschool were interrogated using coercive techniques and produced increasingly bizarre allegations of Satanic rituals, animal sacrifice, and secret tunnels. No physical evidence was ever found.
The Pattern of Contradiction: What the Evidence Actually Shows
Here is where cold logic and pattern recognition become essential. The SRA/RSA debate presents a paradox: there is documented evidence of government mind control programs, organized child abuse networks, and the moral panic that led to false allegations. All three are true simultaneously.
The pattern that emerges is not one of simple truth or falsehood, but of conflation and obfuscation. The existence of real abuse, including organized abuse networks and government experiments, was seized upon by therapists and fundamentalists who built elaborate Satanic conspiracies that could not be substantiated.
When these conspiracies collapsed, they took the legitimate evidence with them. The institutions that had conducted the experiments and protected the abusers were able to hide behind the panic they had helped create.
Part IV: The Suppressed Dimensions of MK-Ultra

The CIA's MK-Ultra program was officially terminated in the early 1960s, but the full scope of its activities remained hidden until the mid-1970s, when congressional investigations exposed its existence.
What followed was even more revealing: in 1973, as Sidney Gottlieb's patron Richard Helms was being removed as CIA director, Gottlieb drove to the CIA records center and ordered the destruction of boxes containing MK-Ultra records.
The destruction was so effective that only fragments remain. We will never know the full human cost. The Chinese state media investigation notes that "the Americans are very good at hiding information. What happened after 1973 remains classified."
The Continuity Question: Did MK-Ultra Really End?
The official narrative is that MK-Ultra ended because it failed. Gottlieb could never figure out how to "insert a new mind" into the void he had created. The program was abandoned.
But survivors and researchers argue that this narrative is itself a cover story. The techniques developed in MK-Ultra did not disappear; they were transferred to other agencies, other programs, other contexts. The recruitment of Nazi and Japanese war criminals provided a ready-made scapegoat: if the programs were ever exposed, the blame could be placed on "those Nazi doctors."
The existence of SRA and RSA networks, with their sophisticated programming techniques, suggests that the knowledge was not lost. And the destruction of records in 1973 suggests that someone wanted the truth to die with the documents.
The "Foreign Expert" Narrative as Strategic Misdirection
For decades, the story of how the United States developed mind-control capabilities has been told in a particular way: Nazi doctors were brought over under Operation Paperclip; Japanese Unit 731's vivisectionists were given immunity; the CIA built MK-Ultra on the foundations of fascist science. This narrative is so widely repeated that it has become the default explanation.
A cold-logic analysis suggests that this story may itself be a piece of the cover-up. The chronology doesn't match: the CIA's interest in psychological warfare predates the large-scale recruitment of German and Japanese scientists.
The methodology was already domestic: LSD, electroshock, sensory deprivation were not secret Nazi inventions but extensions of American psychology and psychiatry. And the recruitment served a different purpose: it provided a ready-made scapegoat if the programs were ever exposed.
The CIA didn't need to import monsters. The monsters were already homegrown. But by pointing the finger at the Nazis and the Japanese, they ensured that the real source of the methodology—the military-industrial-academic complex, the deep American tradition of using vulnerable populations as experimental subjects—remained in the shadows.
Part V: Pattern Analysis & Systemic Logic

Abuse doesn't follow a neat, straight pattern. Rather, it spans a continuum. At one end, abuse occurs without an articulated external purpose beyond maintaining family hierarchy and enabling continued access to victims.
Further along the continuum, abuse is deliberately structured to create fragmented identities (dissociation) and conditioned obedience, sometimes within networks that extend beyond the immediate family; a dynamic that appears in certain court records involving organized crime families, cults, and intelligence‑linked abuse cases.
Across survivor testimony, declassified documents, and investigative journalism, seven patterns emerge consistently.
Pattern 1: Multi-generational involvement
Survivors consistently describe abuse that spans generations within families, with children being abused by parents who were themselves abused as children. This pattern is documented in cases outside the SRA/RSA context, including royalty/nobility and organized crime networks.
The 1998 West Country Incest Case (UK)
An elderly couple were at the center of a network that abused their own children over 35 years. Crucially, as those children grew into adults, some of the victims became abusers themselves, continuing the cycle with their own children and nieces.
The abuse involved seven children and later, their grandchildren. The grandfather was described by the judge as the "prime mover," while the grandmother would select children for abuse and hold them down during rapes.
Nine family members and associates were jailed. The grandfather received 25 years, and the grandmother received 14 years. In sentencing the couple's second son (who received 14 years), the judge noted he had been "abused and encouraged to abuse as a boy."
The Goler Clan (Nova Scotia, Canada)
This is a historic and widely cited case of inter-generational abuse within an isolated rural community. Investigators in the 1980s found that forced incestuous relationships had been taking place for multiple generations. The family lived in extreme isolation, which forced them to "look inwards for support."
Adults openly admitted to engaging in sexual acts with children as young as five. Sixteen adults were charged with hundreds of offenses. Thirteen adults received jail sentences. The case highlighted how social isolation can contribute to the multi-generational cycle of abuse.
The 2025 West Sussex Family (UK)
This is a very recent and harrowing case (convicted in late 2025) involving three generations of a single family. The victim was abused by her grandfather, father, and two brothers. This represents three generations of perpetrators within the same household actively abusing one child.
The abuse began when the victim was six and lasted until she was 12. It included rape, beatings with horse whips, and being locked in a cupboard. When she reported the abuse to her mother, the mother burned her and rubbed salt in the wounds.
Six family members (including the mother, father, grandfather, two brothers, and an uncle) were convicted on 39 counts. They are awaiting sentencing.
These three cases document the pattern of multi‑generational involvement; abuse passed from parents to children, who later become perpetrators themselves.
However, they primarily illustrate the intrafamilial sexual abuse end of the spectrum, where the objective is often to maintain secrecy, enforce family loyalty, and satisfy predatory impulses within a closed system.
They do not publicly document the additional layer of organized mind control intended to turn victims into operatives for external missions, which is a distinguishing feature in some SRA/RSA and organized crime narratives.
Pattern 2: The use of dissociation as a control mechanism
The creation of dissociative identities through trauma is a documented psychological phenomenon. Survivors describe being deliberately split into "alters" with specific functions: the sexual alter, the violent alter, the child alter, the amnesiac alter who knows nothing.
However, it is important to note that unlike the multi‑generational abuse cases previously discussed, there is no single high‑profile criminal trial that publicly documents this specific control mechanism in the same way.
Instead, the evidence comes from clinical literature, survivor accounts documented by specialists, and case studies from law enforcement psychology.
Gaby Breitenbach, Inside Views from the Dissociated Worlds of Extreme Violence (2015)
This book provides clinical case studies of victims who were subjected to organized abuse involving deliberate mind control. Breitenbach, a psychotherapist specializing in extreme violence survivors, documents:
How perpetrators systematically break victims using sadistic violence
The transition from natural dissociation (as a survival response) to programmed dissociation through conditioning
Case material revealing how victims were used in pornography, prostitution, and were "degraded to nothing more than objects, abused at the push of a button according to the desires of the tormentors"
The structural model distinguishing between dissociation as organic response versus deliberately engineered internal control systems
The author explicitly addresses how the "false memory" movement's rhetoric has been weaponized to protect perpetrators by discrediting survivors' accounts.
Richard J. Loewenstein, MD, "Mind Control Transference in Dissociative Identity Disorder" (ISSTD)
Dr. Loewenstein, founder of the Trauma Disorders Program at Sheppard Pratt Health System and a leading international expert on dissociative disorders, presents clinical case material documenting:
"Mind control (invasion) transference"—where patients believe the therapist's help is actually a covert attempt to gain access to and control their minds
The clinical reality that "coercive control is at the center of the type of extreme, tortuous perpetration that most DID patients report experiencing"
Specific perpetrator profiles, including:
"Sadistic abusers, often in organized groups, with a variety of manifest belief systems, who focus on complete enslavement of victims using extreme torture to dominate, control, completely abase, and humiliate victims, and to create automatic obedience"
Parents with DID who are "psychologically invasive and consciously or not invade the child's mind, often to access, control, or create self‑states"
Perpetrators who use hypnosis and therapy‑like techniques as part of childhood abuse
Loewenstein's clinical casework represents thousands of patients seen over three decades at a major trauma disorders program.
Dr. Daniel M. Rudofossi, Covert Operations Unveiling Organized Crime (2023)
Rudofossi, a New York Police Department "cop doc" (police psychologist), provides documented analysis of how dissociation operates as both a survival mechanism and potential control tool in organized crime contexts. Using the Operation Donnie Brasco case—the FBI's six‑year infiltration of the Bonanno crime family by Agent Joe Pistone—Rudofossi examines:
How trauma shapes "functional dissociation as unconscious adaptation"
The psychological mechanisms that allowed Pistone to survive daily immersion in Mafia violence
Implications for understanding how organized crime groups psychologically manage members and informants
While this focuses on law enforcement operatives rather than abuse victims, it provides documented evidence of how individuals operating within violent organized crime environments utilize dissociative capacities to function; and how similar mechanisms can be weaponized by perpetrators.
The clinical literature establishes that dissociation is used as a control mechanism through several documented pathways:
Verbal abuse conditioning | Research shows severe verbal abuse is "the only specific form of childhood trauma strongly related to dissociative symptoms" and functions to keep victims in submission hierarchies
Conflict-based attachment | Simultaneously activating defense and attachment systems creates "approach toward and flight from the caregiver" conflict, fragmenting identity
Programmed dissociation | Moving from organic dissociative response to conditioned, deliberately structured internal control systems that perpetrators can activate
Intrafamilial dissociative dynamics | Cases document how abusers with dissociative conditions may invade children's minds to "create self‑states that correspond in some way to their own"
It is essential to acknowledge that the use of dissociation as a deliberate control mechanism—particularly in organized abuse contexts—has been the subject of intense professional debate.
The Borawick v. Shay (1995) case represents a landmark legal decision where the court excluded hypnotically influenced testimony about satanic ritual abuse. The case involved Joan Borawick, who recovered memories during therapy of childhood abuse that she alleged included cult involvement. The ruling reflected judicial skepticism toward recovered memories of organized abuse.
Similarly, the Patty Burgus case resulted in a $10.75 million settlement against psychiatrist Dr. Bennett Braun, who had treated her for dissociative identity disorder and satanic ritual abuse memories. Braun's license was suspended, and the case became a flashpoint in the "recovered memory" wars.
These controversies do not negate the clinical documentation from specialists like Loewenstein and Breitenbach, who continue to treat patients with histories of organized, programmed abuse. Rather, they highlight that:
The existence of perpetrators using dissociation as a control mechanism is clinically documented in treatment settings
The evidentiary standard for such claims in court remains extremely high
Iatrogenic (therapist‑induced) false memories have been documented in some cases, creating a complex landscape where genuine organized abuse survivors face credibility challenges
The cases and literature above span a continuum that requires distinction.
At one end, dissociation occurs as a natural, unconscious survival response to overwhelming trauma; the brain's built‑in protective mechanism. This appears in the verbal abuse research and many child trauma cases.
At the other end, dissociation is deliberately engineered by perpetrators as a control mechanism. This involves:
Using trauma to fragment identity deliberately
Creating internal "parts" or states that perpetrators can activate
Conditioning obedience through the association of specific triggers with programmed responses
Establishing systems where victims can function externally while internal control structures remain intact
The Loewenstein material and Breitenbach's case studies document the deliberate engineering end of this spectrum. The Donnie Brasco analysis provides insight into how functional dissociation operates in organized crime environments, offering a parallel understanding of how these mechanisms function in high‑control settings.
Pattern 3: Filming as blackmail
Survivors consistently report that their abuse was filmed, and that the footage was used to control them and others.
Let's go over three documented cases where perpetrators filmed abuse and used the footage for blackmail and control. These come from court records, official government sources, and verified news reporting of criminal proceedings.
Australia: DPP v Valentino (ACT Supreme Court, 2024)
A 54-year-old man sexually abused a vulnerable 15-year-old girl who was staying at his home. The abuse was not filmed, but the case demonstrates the blackmail mechanism as a tool of control: the offender used the victim's dependence and his authority over her boyfriend's release from detention to coerce compliance.
The offender told the victim he had control over whether her boyfriend (his son) would be released from juvenile detention. He asked: "What would you do for my son?" and then explicitly stated: "If you give me head, I will let Tom out and you guys will be fine."
The offender pleaded guilty to one count of sexual intercourse with a person under 16. The ACT Supreme Court noted this was a "very serious example" of the offence, describing how the offender "effectively blackmailed her into having sexual intercourse with him before repeatedly, over many hours, performing other sexual acts upon her."
This is an official Australian Capital Territory Supreme Court judgment [2024] ACTSC 140, representing a fully documented judicial finding.
United Kingdom: R v Raducanu and Bruziene (Maidstone Crown Court, 2025)
A woman was plied with alcohol until she was incapacitated and had no memory of events. Her rapist, Vasile Raducanu, engaged in sexual violence while his partner, Indre Bruziene, filmed through a window. The footage was then used to blackmail the victim.
Bruziene sent the victim the recording, revealing the rape she had no memory of, and demanded £5,000, threatening to share the footage with her family. The judge described this as a "particularly callous and cynical act" designed to cause "very serious distress" and "degradation and humiliation."
Raducanu was jailed for 12½ years; Bruziene received 3 years and 3 months. Judge Oliver Saxby KC noted the couple "hatched" a plan for him to engage in sexual activity and for her to film it, with the footage then weaponized for extortion.
This case was extensively documented in Kent Online following the August 2025 sentencing, with direct quotations from the judge's remarks and the victim impact statement.
United States: Erik Lee Madison, 764 Network (Maryland Federal Court, 2026)
Erik Lee Madison, 20, an alleged member of "764"—a violent extremist network—used the internet to sexually exploit at least 10 minors. He created and shared recordings of abuse and used the footage to blackmail victims.
Court documents allege Madison prompted victims to produce sexually explicit content, cut themselves, and mark their bodies with symbols. He extorted victims by threatening to:
Leak the sexually explicit content
Harm victims or their families
Expose victims and family members
Members of the 764 network conduct "coordinated extortions of teens by blackmailing them" using recordings as leverage.
Madison pleaded guilty to sexual exploitation of a child and cyberstalking. He faces a maximum sentence of 40 years, with sentencing scheduled for June 2026.
This case is documented by CBS News based on U.S. Attorney's Office for the District of Maryland court filings, representing a federal prosecution of organized criminal exploitation.
These cases illustrate a spectrum of how filming is weaponized for control:
Direct extortion | Perpetrators film abuse and demand money or continued compliance under threat of release | Raducanu & Bruziene
Authority leverage | Filming not present, but the mechanism of blackmail using a victim's vulnerabilities operates identically | DPP v Valentino
Coordinated network exploitation | Organized groups share recordings and conduct extortion collectively against vulnerable minors | 764 Network
The 764 Network case is particularly significant as it represents an organized criminal structure where filming and blackmail are systematized; consistent with survivor accounts of footage being used not only for individual control but also shared within networks to maintain power over multiple victims.
Pattern 4: The involvement of intelligence agencies
The MK-Ultra documents establish that intelligence agencies were actively researching mind control techniques. The continuity from these programs to organized abuse networks is disputed, but the documented existence of the programs is not.
Let's go over three documented cases or sets of evidence that address the involvement of intelligence agencies in mind control research and the contested continuity to organized abuse networks. These range from officially documented programs to investigated allegations that illustrate the pattern you described.
MK-Ultra — Officially Documented CIA Mind Control Program
MK-Ultra was a covert CIA program launched on April 13, 1953, designed to "manipulate the mental states and brain functions of individuals" through psychoactive substances and other chemical and biological materials.
The program sought to determine whether the agency could "seize a person by remote control in the span of an hour or two and direct him to crash an aeroplane or wreck a train." (The 'mind control' that usually took years for RSA and SRA methods, they sought to achieve in matter of days or months)
The program's existence is undisputed and officially documented. CIA Director Stansfield Turner testified before a joint US Senate committee in 1977 that the project studied "the use of biological and chemical materials in altering human behavior."
Key documented facts include:
The program involved 44 educational institutions, 15 pharmacological and chemical research companies, 12 hospitals and clinics, and 3 prisons
At its peak, the CIA allocated 6% of its total budget to MK-Ultra
Prisoners, civilians, and institutionalized individuals were experimented on without their knowledge
The program operated in multiple countries, including documented experiments at Copenhagen Municipal Hospital involving orphaned children
The program was officially terminated in 1964, but experts note "ample evidence that intelligence agencies continued the project in their domains."
The Finders — Investigated CIA Connection Allegations
The Finders were an intentional community founded in Washington D.C. and Virginia in the late 1960s by former USAF Master Sergeant Marion Pettie. The group came to national attention in February 1987 when two male members were arrested in Tallahassee, Florida for misdemeanor child abuse while traveling with six children who were described as "scruffy," "hungry," and covered in insect bites.
Following the arrests, law enforcement raids on Finders properties uncovered photographs that a confidential police source described as depicting children engaged in "cult rituals," including ceremonial bloodletting and one photograph of a child in chains. The confidential source also claimed the group conducted "brainwashing" techniques.
The case took a significant turn in 1993 when Henry T. "Skip" Clements obtained a report stating that the Washington D.C. police investigation had been dropped as "a CIA internal matter." This led to a Department of Justice investigation after two U.S. representatives, Tom Lewis and Charlie Rose, expressed interest.
The CIA denied involvement. Agency spokesman David Christian asserted the 1993 accusations stemmed from a misunderstanding involving a CIA training contractor, Future Enterprises Inc., where one Finders member worked as a part-time accountant. (If anyone trusts the CIA)
The Outcome:
Florida dropped all charges against the two arrested members after six weeks
Federal authorities concluded "there was no evidence of criminal activity"
The FBI released hundreds of documents on The Finders in 2019, noting it was their "most requested topic"
Scholars (by now, we should know these so-called scholars are just compromised plants) have described the Finders conspiracy theories as an example of the "Satanic panic" that originated broader conspiratorial beliefs about intelligence services and child abuse
The CIA's official denial notwithstanding, the fact that federal investigators were instructed to cease inquiry on the grounds of it being a "CIA internal matter" is documented in the investigative record, making this a contested but formally investigated case of alleged intelligence agency involvement with an organized group involving children.
The Franklin Scandal — Alleged Intelligence-Linked Network
The Franklin child prostitution ring allegations began in June 1988 in Omaha, Nebraska, centering on Lawrence E. King Jr., manager of the Franklin Community Federal Credit Union. Alleged victims claimed that children in foster care were flown to the East Coast to be sexually abused at parties hosted by King, and that the operation involved prominent political figures.
According to investigative journalist Nick Bryant's 2009 book The Franklin Scandal, the case revealed "crucial links between intelligence-led sexual political blackmail operations of the past." (Maybe still 'present,' considering what the Epstein Files revealed in 2026)
The allegations extended beyond King to include:
Claims of a broader network involving GOP lobbyist Craig Spence
Allegations that the operation was designed to compromise high-ranking political figures through blackmail
Conspiracy theories that spread during the investigation claimed the abuse was "part of a widespread series of crimes including devil worship, cannibalism, drug trafficking, and CIA arms dealing"
On July 12, 1990, private investigator Gary Caradori, hired by the Nebraska Legislature's Franklin Committee to investigate the allegations, died along with his 8-year-old son when his plane disintegrated mid-air near Chicago. (A classic CIA signature, allegedly)
Foul play was suspected by Caradori's brother and state Senator Loran Schmit, but investigators did not prove it. No definitive cause for the crash has been established.
The Outcome:
A Nebraska grand jury concluded the abuse allegations were "baseless" and a "carefully crafted hoax," indicting two original accusers on perjury charges (As expected of the compromised judicial system)
A federal grand jury similarly concluded the allegations were unfounded and indicted alleged victim Alisha Owen on eight perjury counts; she served 4½ years in prison
Despite these findings, alleged victim Paul Bonacci filed a civil suit against King and won a default judgment of $1 million in 1999 when King failed to defend himself
King pleaded guilty to embezzling $39 million from the credit union and received a 15-year prison sentence
While the grand juries dismissed the abuse allegations as fabricated, the case is significant because:
It represents a documented instance where child abuse allegations against a politically connected figure triggered conspiracy theories (at this point, conspiracy theories are more trustworthy than "official" statements) about intelligence agency involvement
The death of the lead investigator under suspicious circumstances remains unresolved
The default judgment in Bonacci's favor means a federal judge formally accepted, for civil purposes, that King subjected a child to "organized and directed satanic rituals" and forced participation in a pornography ring
Considering what we now know about Epstein, Lawrence E. King Jr. might as well have been one of the many Epsteins that operate in "elite (degenerate)" circles.
The three cases above represent different categories of evidence that align with our pattern:
MK-Ultra | Documented Program | Declassified CIA records, Congressional testimony, court findings | Undisputed historical fact
The Finders | Investigated Allegation | Police reports, FBI documents, DOJ inquiry, CIA denial | Contested; dropped as "CIA internal matter"
Franklin Scandal | Contested Allegation | Grand jury findings, civil court judgment, investigator death | Abuse allegations dismissed criminally; civil judgment awarded
MK-Ultra establishes that intelligence agencies were actively researching mind control techniques involving unwitting human subjects, including children.
The Finders and Franklin represent instances where allegations of continuity, that these techniques or personnel were integrated into organized abuse networks, emerged and were investigated, though official findings rejected criminal wrongdoing in both cases (as expected).
In the same leg, let's also explore some important cases involving the American Evangelical congregations, which are known to be infiltrated by CIA assets, who leverage them as fronts for illicit activities (allegedly).
Word of Faith Fellowship — Evangelical Cult with "Brainwashing" Allegations
Word of Faith Fellowship is an evangelical church (cult) founded in 1979 in Spindale, North Carolina, by Jane Whaley. The cult has grown to approximately 750 members in North Carolina and nearly 2,000 worldwide, with affiliated churches in Brazil, Ghana, Sweden, and Scotland.
An Associated Press investigation documented that the cult used "money, influence and lies" to separate more than two dozen children from their parents over decades. (This case most closely follows the patterns explored in the Netflix series Wayward)
The mechanisms included:
Social Worker Collaboration: A longtime cult member who served as a county court clerk bypassed the foster system to obtain custody of children from troubled mothers, with judges later describing her conduct as "inappropriate"
Systematic Isolation: Children were educated in private schools, prohibited from watching television or celebrating birthdays or Christmas, and largely isolated from the outside world
Physical Abuse: Former members reported congregants—including pre-teens, toddlers, and crying babies—were regularly punched, choked, and subjected to intense screaming sessions called "blasting" aimed at "casting out demons"
The AP investigation documented clinical assessments supporting claims of coercive control:
A counselor hired by a mother seeking to regain custody of her son conducted a clinical assessment finding the boy showed "signs of being coerced and brainwashed"
The boy reportedly became "hysterical" about missing church services and was "afraid of being 'dealt with'" if he broke cult rules
One mother whose son was taken by cult members told the AP: "One thing that is confusing for people in the community is how these children can be so well-behaved and so well-dressed if things are so bad. But the clothing can cover the bruises and the smiles can hide the hurt"
This case does not involve intelligence agency involvement. Rather, it represents a pattern where cult members exploited existing government systems (courts, social services) through insider positions.
[It is also wise to keep in mind that even the most "trustworthy" press associations are owned by the same families that are often at the top of the elite (degenerate) pyramid leveraging these networks (religious cults, non-profit organizations, so-called orphanages, and so-called charities). So, these press associations are also involved in subverting narrative and blame to protect the one at the top, even if it means scapegoating someone in the middle of the pyramid]
Outcome:
Multiple children were permanently separated from their parents, with some separated for up to a decade
The cult's lawyer disputed all findings, calling allegations "preposterous"
No criminal charges against cult leadership appear to have resulted from the AP investigation
This is a documented American evangelical group with credible evidence of child separation, isolation, control, and clinical documentation of "brainwashing."
George Peters and the Church of Naturalism — CIA Mind Control Claims
George Peters founded the Church of Naturalism, which grew out of a 1960s drug counseling program he ran in Chicago. The church operated from a Hollywood Hills compound described as a "barb wire-ringed, six-acre hilltop complex."
According to a declassified CIA document, Peters claimed direct involvement in the CIA's MK-Ultra mind-control program:
Peters told the Los Angeles Herald Examiner that he had volunteered as a subject in LSD experiments in 1957 while in the Navy
He claimed involvement in two other CIA mind-control programs after his discharge
Beginning in 1977, Peters worked with church secretary Susan Shore on a film exposing the CIA's MK-Ultra program and his role in it
In July 1981, Peters outlined his connection to MK-Ultra at a University of California Santa Cruz symposium titled "The Social and Cultural Implications of Consciousness Research"
The Evidence:
The MK-Ultra connection is documented in declassified CIA records; the agency's own reading room contains a document titled "SLAIN CHURCH FOUNDER PLANNED FILM ON CIA DRUG EXPERIMENTS"
The CIA document confirms Peters claimed involvement in MK-Ultra and was working on an exposé at the time of his death
However, the document notes the newspaper "could not determine whether Peters had ever been in the Navy"
The Outcome:
On November 6, 1982, Peters, 43, and church treasurer James Patrick Henneberry, 31, were found slain in one of two houses on the church compound
Both had been beaten and shot
Police made no arrests in the murders
The CIA acknowledges Peters made these claims. Whether they were true remains unverified. The timing—Peters was murdered while working on a film exposing CIA mind-control programs—has fueled speculation but no confirmed connection to intelligence agencies.
This is a documented case of an American church founder who claimed involvement with CIA mind-control programs and was killed while preparing to expose them.
Michael Woroniecki and Andrea Yates — Evangelical Influence with Mind Control Elements
Michael Woroniecki was a street preacher whose teachings influenced Andrea Yates, the Houston mother who drowned her five children in 2001. Yates was eventually found not guilty by reason of insanity.
The Investigation Discovery docuseries "The Cult Behind the Killer: The Andrea Yates Story" documented how Woroniecki used classic mind control techniques:
Isolation: Woroniecki preached that Satan was embedded in public schools, music, books, and employment, insisting followers isolate themselves. The Yates family began living intermittently on a bus, with Andrea homeschooling the children and limiting contact with the outside world.
Constant Messaging: Woroniecki relied on cassette tapes and VHS recordings to indoctrinate followers, repeatedly reinforcing that the end of days was imminent. One cassette was found with Yates at the time of the tragedy.
Fear-Based Control: Followers were taught that heaven had limited space and doomsday was imminent, fueling ongoing panic.
Corporal Punishment: Former follower Moses Storm reported children were "beaten with pieces of plywood," and Woroniecki demonstrated to followers how to beat children in what he deemed the correct manner.
Evidence of Mind Control:
Woroniecki taught that "violence was seen as a highway to God"
Women were taught they possessed a "witchcraft nature" and that submission to men was mandatory. Woroniecki's wife referred to herself as her husband's "servant"
Correspondence from Woroniecki's wife to Andrea Yates framed Yates as a "bad mother" and warned: "If you allow Satan to come in and still be understanding, the consequences will be tragic"—shortly before the killings
There is no evidence linking Woroniecki to intelligence agencies. Andrea Yates was convicted of murder in 2002, but the conviction was overturned after it was revealed the prosecution's expert had testified falsely about a Law & Order episode. She was acquitted by reason of insanity in a 2006 retrial.
This is a documented case of an American evangelical figure using mind control techniques (isolation, constant messaging, fear) that contributed to a follower's psychotic break. However, there is no child trafficking or intelligence agency involvement.
However, this case shows that there already exist such cults with their own crude mind controlling techniques, and it isn't difficult for intelligence to infiltrate them and use them. They can cut loose when the issue gets too hot, letting the cult take the fall.
Project Monarch, Cathy O’Brien, and the Broader Conspiracy Landscape: In the search for documented cases of intelligence agency involvement in organized abuse (Pattern 4), references frequently appear to individual survivors whose allegations go far beyond the declassified MK‑Ultra record.
The most prominent of these is Cathy O’Brien, who claims to have been a victim of a CIA mind‑control program called “Project Monarch.”
O’Brien first came to public attention with her 1995 book Trance: Formation of America, co‑authored with Mark Phillips. In her account, she alleges:
She was recruited into a mind‑control program as a child, beginning with abuse by her father, who she claims was a CIA operative.
The program—variously called Project Monarch, “MK‑Ultra II,” or simply an extension of MK‑Ultra—used torture, drugs, hypnosis, and ritual abuse to create a dissociative identity structure designed for espionage, prostitution, and blackmail.
She alleges that the program was coordinated by intelligence agencies and reached into the highest levels of government, with victims being used as “sex slaves” and “programmed assassins” for political purposes.
Wikipedia article on O’Brien claims that “despite scholarly investigation of the MKUltra Program, there is no evidence for the existence of Project Monarch except for O’Brien’s testimony.”
No declassified document, court record, or contemporaneous intelligence file has ever been produced to substantiate the existence of Project Monarch as a discrete program. O’Brien’s claims supposedly lacked corroboration, had internal inconsistencies, and aligned with broader satanic ritual abuse (SRA) narratives that were discredited by "major investigations" in the 1990s (the same way Epstein allegations were discredited and he was let go with barely a slap on the wrist by the federal top attorney Alex Acosta until the evidence became too overwhelming to ignore).
O’Brien’s accounts are considered by most "mainstream scholars and journalists" to be part of the “recovered memory” and SRA panic literature rather than historically verifiable fact.
Modern Monarch Conspiracy Theories (Can take them with a grain of salt, without throwing the baby out with the bathwater):
Monarch Tattoos | Conspiracy theorists claim that survivors of the program are often marked with distinctive tattoos; most frequently the monarch butterfly, but also symbols such as barcodes, crescent moons, and certain letters (e.g., “M”). They argue that these tattoos serve as “slave marks” indicating ownership, programming type, or handler identity. These claims have no verifiable evidentiary basis; the same symbols appear widely in mainstream tattooing and popular culture.
Politicians and Celebrities as “Programmed” | Online communities assert that numerous high‑profile political figures, entertainers, and business leaders are “Monarch slaves” or “handlers.” Claims often point to photographs showing a butterfly motif, an odd gesture, or what they interpret as “dissociative glitches” as proof of programming.
“MK‑Ultra Continuity” | Many modern conspiracies assert that MK‑Ultra never ended and evolved into a permanent, global network that continues to produce mind‑controlled operatives. This is presented as fact despite the absence of documentary evidence.
Hollywood and Symbolism | Monarch mythology often incorporates pop culture, claiming that movies, music videos, and awards shows are used to publicly display “programming cues” or to mock victims. The butterfly symbol is frequently cited in such interpretations.
While numerous cases of organized child sexual abuse have been prosecuted (including some with alleged intelligence links, such as the Franklin investigation discussed earlier), none have resulted in judicial findings that validate the existence of Project Monarch or a systematic monarch‑tattoo‑based slave system.
Pattern 5: The protection of the powerful
In every major abuse case, the government, religious institutions, and non-profit organizations protected abusers for decades. The pattern of institutional cover-up is so consistent that it constitutes a predictable system.
The following three cases document the consistent pattern we've identified: institutions systematically protecting abusers for decades, prioritizing reputation over victims, and employing identical cover-up mechanisms across different organizational contexts.
Diocese of Providence (Rhode Island)
The Rhode Island Attorney General released a comprehensive investigation in March 2026 documenting how the Diocese of Providence protected abusers for over 70 years. The investigation examined more than 250,000 pages of documents, including personnel files and internal records from the diocese's "Secret Archive."
Documented pattern:
75 credibly accused clergy abused at least 315 children across seven decades
20 additional abusers were identified whom the diocese had never publicly named
Bishops systematically transferred known abusers rather than removing them; nearly 40 suspected abusers were transferred at least 5 times, some more than 10 times
Five priests alone were accused of abusing a combined 85 children
The report quotes bishops explicitly prioritizing institutional reputation:
Bishop Russell McVinney in 1971 regarding serial abuser Father Marcantonio: "We must by all means avoid scandal"
Bishop Louis Gelineau in 1986 urging a nun to keep quiet: "I certainly want to avoid any further scandal"
Accused priests were sent to church-affiliated "treatment centers" such as the Queen of the Clergy Villa and the House of Affirmation, then returned to ministry. Of 19 diocesan priests placed on leave after abuse allegations, 10 were subsequently returned to active ministry; at least 4 of these went on to abuse additional children.
The Boy Scouts of America
Internal Boy Scouts of America documents known as the "perversion files" or "ineligible volunteer files" were released by court order in 2012 after a lengthy legal battle. The files documented 1,247 men accused of abuse between 1965 and 1985, often with multiple victims. A 2012 LA Times investigation of 1,600 cases revealed systematic cover-up practices.
Documented pattern:
In 80% of cases where the Boy Scouts first learned of abuse, there was no indication they ever called the police
In 100 cases, investigators found "clear indications" of efforts to cover up abuse, conceal it from parents, and keep it from the press
Instead of reporting abusers to police, the Scouts would ask them to resign and help them write cover letters to parents explaining their departure with false excuses ranging from "chronic brain disease" to "duties at a Shakespeare festival."
A scout executive wrote in a 1972 memo about a leader who admitted "acts of perversion with several troop members": "I would like to let this case drop. My personal opinion in this particular case is, 'If it don't stink, don't stir it'"
A scoutmaster accused of sexual assault by a 12-year-old boy in the late 1970s was kept on staff and later recommended for another position by the Scouts, despite documented knowledge of his pattern of abuse. When Humphries was arrested in 1994, he pleaded guilty to sodomizing 20 boys. What never came to light at trial was that the Boy Scouts had known since 1978.
The Boy Scouts' own president acknowledged in 2012: "We definitely fell short — for that we just have to apologize to the victims and the parents and say that we're profoundly sorry. We are sorry for any kid who suffered."
Penn State University
Former FBI Director Louis Freeh led an independent investigation into Penn State University's handling of assistant football coach Jerry Sandusky, who was convicted of sexually abusing 10 boys over 15 years. The Freeh Report, released July 2012, documented systematic concealment by the university's most powerful leaders.
Documented pattern: Joe Paterno (head football coach), Graham Spanier (university president), Tim Curley (athletic director), and Gary Schultz (senior vice president) were found to have "repeatedly concealed critical facts relating to Sandusky's child abuse from the authorities, the Board of Trustees, Penn State community, and the public at large."
In 1998, when police investigated Sandusky for showering with a boy, Vice President Gary Schultz wrote notes questioning the opening of "Pandora's Box" and "More children?" — then took no action. In 2001, a graduate assistant witnessed Sandusky raping a 10-year-old boy in the football facility showers.
Curley, Schultz, and Spanier were prepared to report it to authorities, but after a conversation with Paterno, that changed. Sandusky was granted "emeritus" status in 1999 despite concerns, and his retirement was not forced despite documented incidents.
The Board of Trustees was kept in the dark; in-house counsel Cynthia Baldwin "minimized the seriousness of the investigation" when she briefed trustees.
Outcome:
Sandusky was convicted on 45 counts
Paterno was fired in a telephone call after 61 years at the university
Spanier, Curley, and Schultz faced criminal charges
The university paid out over $100 million to victims
The NCAA imposed unprecedented sanctions
The Freeh Report concluded that Penn State's most powerful leaders engaged in a cover-up to "avoid bad publicity," prioritizing institutional reputation over child protection for over a decade.
Across all three cases, identical elements emerge:
Cover-ups persisted for generations, not isolated incidents
Bishops, university presidents, national organization leaders knew and acted to conceal
Abusers were moved rather than removed, enabling continued abuse
Explicit statements about avoiding "scandal" and "bad publicity"
False explanations, hidden records, minimized reporting
Polygraphs, intimidation, and silencing tactics
Those who spoke out were sidelined
While not included as one of the three main case studies, the Larry Nassar scandal at USA Gymnastics and the U.S. Olympic Committee represents another identical pattern documented in Stanford Business School case studies: a "performance-first culture" that protected a serial abuser for decades while athletes' complaints were systematically ignored.
This case further demonstrates that the pattern spans religious, youth, educational, and athletic institutions alike.
Pattern 6: The conflation of legitimate evidence with panic
Each time allegations of organized abuse have surfaced, they have been met with a combination of denial, dismissal, and—when the evidence becomes too strong to ignore—conflation with the most extreme and unsubstantiated claims.
The result is a manufactured narrative that genuine abuse is merely a “panic,” rendering all evidence suspect and shielding perpetrators behind a wall of ridicule.
The following three case studies demonstrate this pattern in operation.
McMartin Preschool (1983–1990)
In 1983, a parent reported to police that her 2‑year‑old son had been sodomized by teacher Ray Buckey at McMartin Preschool in Manhattan Beach, California. The investigation initially uncovered physical evidence, including a report by a pediatrician documenting anal trauma. Dozens of children subsequently disclosed abuse through structured interviews.
As the case expanded, investigators, under pressure to uncover the full scope, employed suggestive interview techniques that elicited increasingly fantastical allegations: secret tunnels, animal sacrifices, flying witches, and ritual murder. The media saturated the public with these extreme claims.
After six years and the longest, most expensive criminal trial in U.S. history, the jury acquitted all defendants on all charges. The failure to secure convictions was used to declare the entire category of organized abuse a “moral panic.”
Subsequent scholarship, however, has noted that actual abuse occurred at McMartin; the panic label served to erase the credible evidence and protect the institution. A 2025 retrospective noted that “the ‘satanic panic’ narrative… allowed the public to dismiss every claim of organized abuse as hysteria, even when physical evidence existed.”
Kern County Child Abuse Cases (1980s)
Between 1983 and 1986, social workers and police in Kern County, California uncovered widespread sexual abuse of children, often involving multiple family members. Dozens of adults were charged, and many confessed. Physical examinations documented genital injuries consistent with abuse.
As with McMartin, some interviews produced allegations of satanic rituals, animal sacrifice, and bizarre ceremonies. These extreme elements were amplified by local media. When appellate courts later overturned several convictions, primarily due to coercive interrogation tactics, critics seized on the ritual claims to paint the entire prosecution as a witch hunt.
The state of California eventually paid out $10 million in settlements to wrongly convicted defendants. But in the process, legitimate abuse was conflated with the false ritual elements.
A 2021 review of the case files concluded that “while some convictions were unjust, the underlying sexual abuse was real; yet the ‘panic’ label allowed officials to avoid reckoning with the institutional failures that allowed abuse to persist.” The pattern repeated: extreme allegations were used to invalidate the entire evidentiary base.
The 2026 DOJ Epstein Files Disclaimer
In 2026, the Department of Justice released thousands of pages of Epstein-related files under the Epstein Files Transparency Act. Among them were FBI interview summaries containing detailed allegations of ritual abuse, sacrifice, and cannibalism (e.g., file EFTA00147661). These raw materials were part of the federal investigation.
The DOJ appended an unusual disclaimer stating: “The files contain raw allegations from the public. Some content may be false or fraudulent.”
This preemptive warning, amplified by media, created a framework in which all evidence, including non‑ritual abuse documentation, could be dismissed as part of a “conspiracy theory.”
The disclaimer was used to discredit the entire file release, despite the fact that many documents contained mundane, corroborative evidence of trafficking.
Within weeks, mainstream outlets began characterizing the ritual allegations as the “real story” of the files, while ignoring the hundreds of pages documenting the operation’s institutional network.
The effect was to conflate legitimate evidence of systemic abuse with the most extreme, unsubstantiated claims, exactly the pattern seen in McMartin and Kern County. The disclaimer itself became a tool to inoculate the government from accountability by framing all files as inherently suspect.
How the Pattern Operates (Phase | Mechanism | Example):
Legitimate evidence emerges | Victims disclose; physical findings; documents surface | McMartin pediatrician report; Kern County medical exams; Epstein files with flight logs
Investigation expands | Pressure to uncover scope leads to suggestive methods or inclusion of raw, unverified tips | McMartin interviews; Kern County interrogations; DOJ collecting all public tips
Extreme allegations surface | Ritual, sacrifice, cannibalism, tunnels, etc. | McMartin “secret tunnels”; Kern County satanic cult claims; Epstein file cannibalism allegation
Media amplifies extremes | Outlets focus on sensational elements, ignoring core evidence | McMartin media circus; 2026 headlines on “Epstein cannibalism”
Official dismissal | Authorities use extreme claims to discredit the entire case | Acquittals in McMartin; Kern County convictions overturned; DOJ disclaimer
Long‑term narrative | “Satanic panic” label applied retroactively, erasing credible evidence | Scholarly work now shows real abuse occurred, but public memory is “panic”
This pattern serves a clear institutional purpose: by associating legitimate evidence with the most extreme, least credible allegations, authorities can dismiss all of it without addressing the underlying system of abuse. The pattern recurs across decades because it works:
Prosecutors avoid difficult cases by labeling them “mass hysteria.”
Institutions escape liability by blaming “overzealous investigators.”
The public learns to mock any organized abuse claim as “satanic panic.”
Perpetrators remain protected.
This analysis does not assert that every extreme allegation is true. Rather, it documents the mechanism by which institutions systematically conflate verifiable abuse with unverified claims to discredit the whole. The effect is that survivors of documented abuse, including those with physical evidence, are painted as part of a “panic,” while networks of abusers continue to operate.
Pattern 7: The strategic deployment of a foreign scapegoat
When institutions engage in wrongdoing that might be traced back to their own culture or leadership, they often construct an external "evil" that is blamed. The Nazi-import story serves this function. So does the "Satanic cult" narrative in the SRA panic.
This pattern serves multiple functions: it absolves domestic institutions, channels public outrage toward a foreign or ideologically distant target, and allows the underlying systemic failures to remain unexamined.
The following case studies illustrate how this scapegoating mechanism has operated across different historical contexts.
Operation Paperclip and the Nazi‑Import Narrative
At the end of World War II, U.S. intelligence and military agencies engaged in a systematic effort to recruit Nazi scientists, engineers, and intelligence operatives. Over 1,600 German scientists were brought to the United States under programs like Operation Paperclip, with the explicit goal of gaining technological and intelligence advantages in the Cold War.
Declassified documents show that U.S. officials actively concealed the Nazi past of these recruits. The Joint Intelligence Objectives Agency (JIOA) erased incriminating records, fabricated biographies, and granted security clearances while the US government and the press accused them of slave labor and medical atrocities.
Wernher von Braun—not unlike how the US had used patients in mental institutions for MK-Ultra experimentations—had used concentration camp labor for his V‑2 rocket program; but his SS affiliations were scrubbed from official files.
When public awareness of these operations surfaced, the narrative was consistently reframed: the “evil” was cast as the Nazi regime itself, a "foreign pathology" that had been defeated. American institutions were portrayed as pragmatically salvaging useful knowledge from a vanquished enemy, not as perpetuating or integrating that evil.
The U.S. intelligence claimed it had just adopted Nazi human‑experimentation methodologies (later evident in MK‑Ultra), while obscuring its own intentional participation in these inhumane projects.
By treating the Nazi scientists as isolated foreign assets rather than as conduits of a system that was being absorbed, the U.S. government avoided scrutiny of how its own agencies had embraced the very techniques for which they had condemned the Nazi regime.
The “Nazi evil” remained safely quarantined in the past, even as its practitioners became pillars of American power.
The “Satanic Cult” Narrative in the SRA Panic
In the 1980s, legitimate cases of child sexual abuse emerged; some involving organized networks, as documented in cases like the McMartin Preschool and Kern County. Physical evidence and victim disclosures indicated that abuse had occurred, often within families and institutions.
As investigations expanded, authorities and media constructed a narrative of vast, shadowy “satanic cults” that supposedly kidnapped and ritually sacrificed thousands of children. This externalized “evil” was portrayed as a secret society operating outside mainstream culture; a foreign intrusion into otherwise wholesome communities.
The “cult” narrative served to deflect attention from the documented reality that most abuse occurred within families, religious cults, and trusted institutions; not via anonymous satanists.
When the more extreme allegations (flying witches, secret tunnels) failed to yield convictions, the entire category of organized abuse was dismissed as a “satanic panic.” The scapegoat, the external satanic cult, became the focus of debunking, allowing the underlying abuse that had been documented to be swept aside.
A 2025 retrospective noted: “The satanic cult narrative was a convenient fiction that protected real abusers by turning the public’s attention to an imaginary enemy.”
Perpetrators within families, religious institutions, and youth organizations continued to operate with impunity. The scapegoat had served its purpose: the “evil” was safely located in a mythical external cult, and the institutions that had protected abusers were never held to account.
The “Russian Disinformation” Frame in the Epstein Files
In 2026, the Department of Justice released thousands of pages of Epstein‑related files under the Epstein Files Transparency Act. Among the materials were FBI interview summaries containing unverified allegations of ritual abuse, international political figures, and extreme violence; alongside mundane documents confirming the scope of Epstein’s trafficking operation and his network of powerful associates.
Within days of the release, media outlets and government officials began emphasizing a new narrative: that the most sensational allegations were part of a “Russian disinformation campaign” designed to destabilize American institutions. The DOJ’s own disclaimer, warning that “some content may be false or fraudulent,” was used to bolster the claim that foreign operatives had seeded the files.
By attributing the problematic portions of the files to a foreign adversary, the government achieved multiple objectives:
Domestic institutions (the DOJ, FBI, State Department) were absolved of responsibility for any failings in the Epstein investigation.
The public was encouraged to view the entire file release with suspicion, conflating the disinformation claim with the entire evidentiary record.
Calls for further investigation into powerful figures whose names appeared in the files were dismissed as falling for “foreign propaganda.”
Just as the “satanic cult” narrative externalized abuse onto a mythical enemy, the “Russian disinformation” frame externalized accountability for the Epstein network onto a geopolitical adversary. In both cases, the scapegoat allowed corrupt American institutions to avoid confronting their own complicity.
What These Patterns Reveal?
The seven patterns examined across these case studies were not selected arbitrarily. Each represents a documented mechanism of concealment that, when viewed in isolation, might be explained away as institutional incompetence, isolated corruption, or historical accident.
Yet the recurrence of these patterns—across religious institutions, youth organizations, universities, government agencies, and intelligence programs—reveals something more systematic. If any one pattern required active suppression, the institutions involved would need to coordinate denial, control information, and manage public perception.
The fact that all seven patterns operate in parallel, across decades and jurisdictions, suggests a level of orchestration that cannot be sustained without the implicit or explicit backing of the highest levels of government, including the justice system itself.
The Epstein case is not an exception to this rule; it is the culmination. In that single network, we see multi‑generational involvement (Pattern 1), the use of dissociation and trauma as control mechanisms (Pattern 2), filming as blackmail (Pattern 3), documented intelligence‑adjacent operations (Pattern 4), institutional protection of the powerful (Pattern 5), the conflation of evidence with panic (Pattern 6), and the strategic deployment of a foreign scapegoat (Pattern 7).
Yet Epstein received a non‑prosecution agreement in 2008, died in federal custody under circumstances that remain legally disputed, and his files were released only under congressional compulsion (only half); each step a demonstration that the same institutions tasked with accountability were themselves entangled in the network.
What the convergence of these seven patterns demonstrates is that the question is no longer whether such a system exists, but how it continues to operate despite intermittent exposure.
The case studies collected here, each drawn from court records, official investigations, and declassified documents, show that efforts to hide these patterns are not isolated failures but coordinated strategies.
When a network employs all seven, with the apparent protection of the justice system and the highest agencies of government, the absence of accountability is not a flaw; it is the design. Epstein’s island was not an aberration; it was a mirror.
Epstein, A Product of MK-Ultra II (Monarch)?
Let's now examine the Epstein case through the analytical lens of Project Monarch—treating the available documentation not as complete truth, but as data points that can be assembled into a pattern.
This approach accepts as its starting assumption that the institutions controlling the release of information (governments, mainstream press, scholarly gatekeepers) are themselves part of the system being examined. The question is not whether the official narrative is true, but what patterns emerge when the documented fragments are viewed through that frame.
The Rothschild Connection: Documented Links
The Epstein files released by the U.S. Department of Justice in 2026 contain multiple references to the Rothschild family that fit the pattern.
According to the files, Ariane de Rothschild, CEO of the Edmond de Rothschild Swiss private bank, which oversees approximately $236.8 billion in assets, exchanged dozens of emails with Jeffrey Epstein over roughly five years. The correspondence included:
Arrangements for multiple meetings at Epstein's homes in New York and Paris
An invitation for de Rothschild to stay at Epstein's apartment
References to personalized candles with Epstein's "favorite mathematical formula" made for him "only"
A 2016 exchange where de Rothschild mentioned being sick with the flu and referred to an individual identified only as "B" whom she was "tired of handling" (Benjamin de Rothschild, her husband, died five years later from a heart-attack) [Or, it could just be Macron's handler, Bridgette Macron. I'm kidding. Maybe]
The files also describe a claimed 2015 agreement involving Epstein's Southern Trust company and a Rothschild firm for $25 million in risk analysis and algorithm services. A document dated October 5, 2015, is described as linking the payment to "issues between the U.S. and the Rothschild firm."
One email exchange in the document cache alleges that when Adolf Hitler was destitute in Vienna, he stayed in a shelter said to have been funded by both the Rothschild and Epstein families. Whether this is historically verifiable is less relevant than the pattern it represents; the files themselves contain this claim, positioning the Epstein and Rothschild names together across generations.
The Macron Connection: Rothschild Origins
The conspiracies regarding Emmanuel Macron being "picked from a Rothschild organization" aligns with documented facts about his career trajectory. Macron worked as an investment banker at Rothschild & Cie Banque from 2004 to 2008, where he became a partner and worked on high-profile deals including the Nestlé-Pfizer acquisition.
The Epstein files show Macron's name appearing in multiple records before and after his 2017 election, with Epstein allegedly claiming he sought Macron's help on various matters.
Whether this represents anything more than a powerful financier seeking access to an emerging political figure is open to interpretation, but the pattern—a figure elevated from a Rothschild institution to political leadership, maintaining connections to the Epstein network—is consistent with the Monarch model we're exploring.
The "Selection" Pattern: Epstein's Mysterious Rise
The documented history of Epstein's wealth accumulation contains anomalies that fit the "selected" rather than "earned" pattern.
Supposedly born to working-class parents in Brooklyn, Epstein never graduated from college but was hired to teach mathematics and physics at the prestigious Dalton School in Manhattan in the mid-1970s; despite lacking formal credentials.
He was fired for "poor performance," but not before supposedly "impressing a parent" who was a senior executive at Bear Stearns, leading to his hiring at the investment bank.
According to Forbes analysis of court filings, Epstein accumulated an estimated $578 million fortune by the time of his death. The majority came from just two clients: Leslie Wexner (Victoria's Secret founder) and Leon Black (private equity investor), who together paid Epstein approximately $370 million in "fees."
A 2025 analysis concluded these two clients accounted for up to 75% of his fee income between 1999 and 2018.
Wexner gave Epstein "power of attorney over his life" in the 1990s, allowing him to sign Wexner's name on checks, hire staff, and manage his personal affairs. When the relationship ended, Epstein left with a significant portion of his wealth; though the exact mechanism remains unproven.
This pattern—a figure who mysteriously acquires vast wealth after being "selected" by someone higher up through a predecessor—applies not only to Epstein but also to Wexner himself, and potentially to the generation before him.
When examined as a multi-generational chain, the Wexner family fortune reveals a repeating structure: an immigrant or outsider is elevated through connection to an established figure, then later elevates a protégé in turn (all clearly interwoven with intelligence agencies, especially the CIA and Mossad).
The asset in the generation before Wexner in Epstein's line of assets was likely Bella Cabakoff, Les Wexner's Mother. She emigrated from Russia to Columbus, Ohio in 1912 with her parents "to escape persecution."
At age 21, Cabakoff became the "youngest buyer" for the Lazarus department store chain, a prominent retail institution in Columbus. This position placed her inside an established commercial power structure, giving her access, expertise, and connections that would later enable the family's ascent.
After spending over 20 years at Lazarus, she and her husband Harry Wexner opened a women's clothing store named "Leslie's" (after their son) on State Street in Columbus in 1951. This store became the "training ground" for Leslie Wexner.
When Leslie opened his first Limited store in 1963, his parents closed their own store to join his venture. Bella served on The Limited's board for 34 years, from its founding in 1963 until 1997, and remained a close adviser to her son until shortly before her death in 2001.
The documented facts of Wexner's start contain elements that fit the "selected" pattern:
In 1963, Wexner borrowed $5,000 from an aunt and another $5,000 from a bank to open the first Limited store. While presented as a modest entrepreneurial beginning, this capital injection from a family network enabled the initial launch.
The store grossed $162,000 in its first year, exceeding the $100,000 goal. Within six years, Wexner opened six stores in Columbus alone. By 1969, he took the company public.
In the 1980s, Wexner's Limited Inc. acquired Victoria's Secret (1982, for $1 million), Lane Bryant (1982), Henri Bendel (1985, $10 million), Lerner Stores (1985, $297 million), and Abercrombie & Fitch (1988, $46 million). These acquisitions, often made at prices that proved spectacularly undervalued, built an empire that by 2006 reported $9.7 billion in annual revenue.
As documented in the previous section, Wexner's relationship with Epstein mirrors the same structure:
In the 1980s, insurance executive Robert Meister introduced Epstein to Wexner, recommending him as a financial adviser. Wexner, who was building his retail empire, drafted Epstein to help with investments.
In 1991, Epstein obtained power of attorney over Wexner's personal finances, enabling him to buy and sell assets on Wexner's behalf with "virtually no oversight." Epstein allegedly sold himself a New York home and a private plane that had belonged to Wexner at "deeply discounted price."
When Wexner's wife took over family finances amid the 2008 Epstein investigation, she discovered Epstein had misappropriated funds to the tune of "several hundred million dollars." Epstein agreed to repay $100 million as part of a settlement that year; the same year Epstein pleaded guilty to soliciting a minor.
Wexner now calls Epstein a "world Olympic con artist" who "stole vast sums" from his fortune and says he was "conned."
The pattern invites questions that official sources do not answer:
How did Bella Cabakoff, a Russian immigrant, become the youngest buyer at Lazarus; a position that required access and sponsorship? Who selected her?
How did a man who started with a $10,000 loan build a $9.7 billion retail empire in one generation; acquiring Victoria's Secret for $1 million, a fraction of its eventual value?
Why did Wexner grant Epstein, a former math teacher with no financial credentials, unprecedented power of attorney over his entire fortune?
When Wexner describes Epstein as a "con artist" who stole "hundreds of millions," why did the settlement involve Epstein paying back $100 million rather than facing prosecution for theft? Was it funds to be transferred to the next asset after him?
As with the Epstein-Rothschild-Macron pattern, the official narrative explains these as coincidences, bad judgment, or isolated criminality. The pattern-based alternative, that Wexner was himself "selected" and later served as a conduit to the next "selected" (Epstein) in turn, rests on the same documented facts, interpreted through a different lens.
In 1996, five years after being conferred with a substantial portion of Wexner's wealth, Epstein became a resident of the U.S. Virgin Islands, establishing his only revenue-generating entities there to benefit from tax exemptions.
In 1998, he purchased Little Saint James, later known as "Epstein's Island," for approximately $8 million. This pattern of jurisdictional arbitrage and asset protection is consistent with intelligence-linked financial operations.
Two days before his death in August 2019, Epstein signed a 32-page trust document named the "1953 Trust"—the year of his birth. The trust named:
Karyna Shuliak (a Belarusian dentist 40 years his junior) as primary beneficiary, slated to receive approximately $100 million
Darren Indyke (longtime personal lawyer): $50 million
Richard Kahn (in-house accountant): $25 million
Mark Epstein (brother): $10 million
Ghislaine Maxwell (co-conspirator): $10 million
Over 40 other beneficiaries, many redacted
The timing—a comprehensive estate plan executed 48 hours before an alleged suicide in federal custody—is anomalous by any standard.
Karyna Shuliak, the Belarusian dentist named as the primary beneficiary of Jeffrey Epstein's $600 million estate, occupies a unique position in the Epstein saga. She was the last person he called from jail, received $100 million in his 1953 Trust, and was given a 33-carat diamond ring "in contemplation of marriage."
Yet she also appears, on paper, to be a singularly unlikely heir to a sophisticated global intelligence-adjacent operation.
The question is whether she represents the genuine "next chosen one" in the chain of wealth and power transmission; or whether she was deliberately positioned as a decoy to shield Epstein's true successor.
Profile: Who Is Karyna Shuliak?
Relationship | Supposedly Epstein's favored girlfriend
Origin | Belarus, arrived in US around age 20 (2010)
Age Difference | 36 years younger than Epstein (born 1990)
Known Since | At least 2012
Education | Dental studies at Columbia University—admitted through "irregular process" coinciding with Epstein fundraising
Nickname | Called "the inspector" for her tendency to monitor Epstein's activities
Last Contact | The last person Epstein called from jail before his death
Current Status | Lives in Manhattan apartment owned by Epstein's brother Mark
Several documented facts suggest Shuliak may be a deliberately conspicuous figure designed to absorb public attention while Epstein's true successors operate in the background.
A "selected one" in the pattern we've traced (Wexner, Epstein, etc.) typically emerges through institutional channels—banking, intelligence, elite finance. Shuliak's profile is jarringly different:
She arrived from Belarus at 20 with no evident family connections to power networks
She required Epstein to orchestrate her admission to dental school through donations and back-channel arrangements
Her immigration was managed through what victims' lawyer Sigrid McCawley described as Epstein's pattern of using "sham same-sex marriages" to obtain citizenship for women he wanted to keep in the country
She referred to Epstein in emails as "the purest man out of all men"—language that suggests a groomed dependent, not an equal or successor
A genuine heir to a covert financial-intelligence apparatus would presumably have existing institutional standing, not require the outgoing principal to arrange her dental school admission.
The 1953 Trust was signed 48 hours before Epstein's death, when he was in federal custody facing sex trafficking charges. This timing strongly indicates defensive estate planning rather than deliberate succession:
By placing assets in a trust in the U.S. Virgin Islands (a jurisdiction known for strong asset-protection laws), Epstein created a legal structure that victim compensation funds, tax authorities, and civil litigants would need to navigate for years
Shuliak's $100 million designation, along with Indyke and Kahn's combined $75 million, functions as a creditor shield: funds allocated to named beneficiaries are harder for victims to claim than if assets remained in probate without designated heirs
Estate lawyer Daniel Weiner confirmed that no beneficiary will receive anything until all victim claims are satisfied; meaning Shuliak's inheritance is contingent on a process that has already paid out over $150 million to victims
If Shuliak were Epstein's true chosen successor, her inheritance would be structured to actually reach her, not left subordinate to a multi-year compensation process that has already drained the estate from $600 million to approximately $120 million.
The trust's other major beneficiaries—Darren Indyke ($50 million) and Richard Kahn ($25 million)—are far more plausible successors in the pattern we've identified:
Indyke was Epstein's longtime personal lawyer; Kahn was his in-house accountant
Both are named co-executors of the estate, giving them control over the trust's administration
They established and managed the victim compensation fund, positioning them as gatekeepers to all claims against the estate
Unlike Shuliak, they have the professional expertise to manage complex offshore structures, real estate holdings, and investment portfolios
If Epstein's network continues to operate, it would almost certainly do so through Indyke and Kahn, the men who control the legal and financial infrastructure, not through a Belarusian dentist whose primary qualification was being "the last person he called."
If Shuliak were a decoy, her carefully documented paper trail—the emails, the donations, the "irregular process"—would function as designed: it gives journalists and investigators something to find, a narrative to publish, and a figure to scrutinize, leaving the real machinery untouched.
Shuliak's designation as primary beneficiary serves two functions simultaneously: By naming a specific individual (Shuliak) along with Indyke and Kahn, the trust creates designated claimants who must be satisfied before general creditors. This is a standard strategy for shielding assets from lawsuits.
A Belarusian dentist inheriting $100 million is a compelling story. It directs media attention to a figure with no institutional power and no ability to perpetuate Epstein's network. The real infrastructure—the offshore accounts, the real estate holdings, the client relationships—remains controlled by Indyke and Kahn, the co-executors.
The monarch framework posits that individuals are not simply wealthy or powerful by accident, but are "selected" through established family networks and multi-generational arrangements.
In the interpretive framework we're working with, these documented connections are not coincidental social ties but evidence of a structured system where:
Certain family bloodlines (Rothschild being one) serve as nodes in a multi-generational control network
Individuals like Epstein are "selected" and elevated not for merit but for suitability as operatives
Political figures like Macron are "placed" from institutional positions (Rothschild bank) into leadership roles
Financial structures (the 1953 Trust, offshore entities) are designed to maintain wealth and control across generations
The Epstein network operated as an intelligence-gathering and blackmail apparatus, not merely a sex trafficking operation
When examining these cases, one must assume that the same institutions involved in these operations also control the information environment around them.
The FBI concluded that "no evidence incriminating third parties" exists and that Epstein "definitely" died by suicide, despite extensive documented contact between Epstein and powerful figures.
The Justice Department initially claimed a "client list" existed, then stated no such list existed. Key beneficiary names in the 1953 Trust remain redacted in official releases. The DOJ removed full download links shortly after initial publication, requiring piecemeal reconstruction of the files.
The absence of conclusive evidence in official sources is not evidence of absence; it is evidence of the system's capacity to control what becomes "official." The same agencies that conducted MK-Ultra, that destroyed the records in 1973, that allowed Epstein to serve 13 months with work release in 2008, are the same agencies now certifying that nothing more is there to find.
Parallels Across MK-Ultra/Monarch Cases:
Family Selection | Multi-generational programming bloodlines | Rothschild correspondence; Maxwell family ties (Robert Maxwell alleged Mossad connection)
Financial Elevation | "Picked" operatives given resources | Epstein's mysterious wealth from two patrons; $25M Rothschild agreement
Blackmail Infrastructure | Compromat as control mechanism | Alleged filming operation; "commodity of exchange" structure
Institutional Positioning | Operatives placed in key roles | Macron: Rothschild → Presidency; Epstein: education → finance → intelligence adjacency
Death in Custody | Elimination of compromised assets | August 10, 2019: suicide with unmonitored cell; guards reportedly falsified logs
Record Destruction | Information control | 1973 MK-Ultra files destroyed; 2026 redactions; "client list" existence disputed
Whether these documented fragments constitute evidence of a coherent "Monarch" system depends on the interpretive framework applied. Official sources will never validate the framework; by the logic of the pattern itself, they cannot, because they are the system being examined.
What can be stated with certainty is that the Epstein files released by the U.S. Department of Justice in 2026 contain multiple data points that align with the pattern we've identified.
The redactions, the disputed existence of a client list, the convenient death in custody, and the Rothschild financial connections are not inventions of conspiracy theory; they are documented in the official releases themselves.
Epstein Island: RSA/SRA Pattern Analysis
The following section examines documented physical evidence, witness testimony, and official records from Jeffrey Epstein's Little Saint James island through the lens of Ritual Sexual Abuse (RSA) and Satanic Ritual Abuse (SRA) patterns.
As with previous sections, the analysis distinguishes between documented physical facts (photographs, blueprints, official records) and allegations contained in legal files (FBI interview transcripts, witness statements) that remain unverified but are part of the official record.
The Temple: Architecture of Ritual
At the southern tip of Little Saint James, atop a cliff facing south, stands a building universally referred to as "Epstein's temple," a structure whose design, placement, and symbolism have drawn sustained scrutiny.
Shape | Cube-shaped with gold dome; originally submitted as octagonal "music hall" in blueprints | Cube = earthly stability/matter; Dome = celestial/heaven; Octagon = transitional shape between physical and spiritual realms in esoteric traditions
Color Scheme | White base, eight large blue stripes, gold dome | Blue/white/gold = stripes historically associated with outcasts, heretics, prisoners
Statues | Three rooftop statues: two golden birds (one bird of prey, one scavenger), one of Poseidon (Greek sea god) | Carnivorous birds = death, consumption, "night wisdom"; Poseidon = sea deity associated with chaos and destruction
Courtyard | Paved perimeter with cement "benches" at cliff edge; labyrinths ground markings | Labyrinths = tools for spiritual initiation and "earth energy" work in occult traditions; benches potentially functioning as altars
Doors | Large wooden arch doors with trompe l'oeil deception technique; locks appearing to be on the outside | "Deceive the eye" = literal deception architecture; locks on outside = spiritual imprisonment symbolism
Interior Division | Single large room with elevated section accessed by single step | Mirrors biblical temple division (Holy Place vs. Holy of Holies) separated by veil
The building's most prominent feature—eight blue stripes on a white background—has been interpreted as carrying specific occult significance:
Octagon as Transition: In esoteric traditions, the octagon is viewed as the intermediary shape between the square (earthly matter) and the circle (divine spirit). It represents a "portal" between physical and spiritual realms.
Inverted Application: Fr. Chad Ripperger, a Catholic exorcist, stated that the layout of Little Saint James "suggests it was heavily involved in occult and satanic ritual activity," with the temple functioning as a "time machine" celebrating death as a portal into eternity.
In a detail noted by multiple sources, the temple's golden dome and statues were "violently ripped off the building during a 2017 hurricane and were never recovered." The storm was named Hurricane Maria. Whether this was coincidence or, as some interpret, "God through nature providing poetic justice" is a matter of perspective.
A piano technician who visited the temple in 2012 reported finding, among the furniture and mattresses, a portrait of Jeffrey Epstein and Ghislaine Maxwell having a papal audience with Pope John Paul II hanging above the grand piano.
The presence of this image in a space used for alleged ritual abuse has been interpreted as either a "trophy" or a symbolic assertion of dominance over institutional Christianity.
Epstein's Attitude Toward Christianity
Documented statements attributed to Epstein align with the temple's apparent anti-Christian symbolism:
After a young girl reportedly called upon Jesus during abuse, Epstein allegedly wrote that she felt God's presence and knew "Jesus watches over her... Whoops!"—mocking her faith.
In a conversation with Steve Bannon, Epstein dismissed Jesus as "just a carpenter" and abruptly ended the discussion.
When Bannon asked if Epstein thought he was the devil himself, Epstein replied with a "creepy grin": "No, but I do have a good mirror."
The Dentist Chair and Masks: Medical Ritual Apparatus
Among the most disturbing images released by the House Oversight Committee in December 2025 were photographs of a room containing a dentist chair surrounded by masks on the walls.
Dentist Chair | Central position in a small room, appears to be medical examination/treatment chair | House Oversight Committee photos, Dec 2025
Masks | "Creepy masks" of male faces hung randomly around bare white walls | Official release
Room Configuration | Small room; what appears to be a window or glass door with wall behind it (fake access point/maybe boarded up later) | Body language expert analysis
Covered Window | Window or glass door appears to have been covered or blocked | Photographic evidence
Body language expert Judi James, analyzing the images for The Mirror, offered the following observations:
The masks "look a bit like hunting trophies"
They are positioned "as though they are watching whatever occurs in that chair in the middle"
The fake access point "can easily make a person feel trapped or uneasy"
Within RSA/SRA frameworks, the combination of a medical examination chair with watching faces (masks) evokes documented patterns where perpetrators:
1. Use medical settings to normalize invasive violation
2. Create surveillance environments where victims feel constantly watched
3. Employ masked figures to depersonalize perpetrators and induce dissociation
The chair was never publicly identified as having legitimate dental or medical function on the island. No licensed dental practice operated from Little Saint James.
Underground Tunnels and Subterranean Structures
Speculation about underground tunnels beneath Little Saint James has circulated for years. Documented references include:
Theoretical Connection: Some theorists have suggested there is a "secret underground tunnel connecting the temple" to other structures on the island. This remains unconfirmed by official documentation.
Bunker-Like Architecture: Body language expert Judi James noted that the interior rooms "appear to have no natural daylight" and "look as though they are in some kind of cellar or bunker."
Painted-Over Atrium: One bedroom features a glass atrium ceiling that "has been apparently painted over to create an oppressive effect," suggesting deliberate concealment of natural light.
Ritual Abuse Allegations in the Epstein Files
The 2026 DOJ release of Epstein files under the Epstein Files Transparency Act contained allegations so extreme they generated international controversy.
A female witness, identified in FBI interview records under file number EFTA00147661, made the following sworn statements:
Ritual Sacrifice | Witness stated she witnessed a "ritual sacrifice" aboard Epstein's yacht
Mutilation | A victim had their feet sheared off with a machete during the ritual
Infant Disembowelment | Witness described the disembowelment of an infant
Coprophagia | Allegations involved consumption of infant intestinal contents
Political Figures | Witness claimed she was raped by a former U.S. President (George H.W. Bush or George W. Bush, depending on translation)
Racialized Abuse | Witness described collective sexual assaults involving victims of different ethnicities
The Department of Justice, when releasing these files, included an unusual "disclaimer" stating: "The files contain raw allegations from the public. Some content may be false or fraudulent."
This disclaimer was necessitated by the Transparency Act, which required release of all materials submitted to the FBI, regardless of credibility. The DOJ has repeatedly stated that "many sensational online claims lack corroboration and do not warrant charges."
2009 Jimenez Video Resurgence: Alongside the FBI interview, a 2009 video of Mexican model Jimenez resurfaced. In the footage, filmed outside a Monterrey hotel, she appears distressed and states: "They eat people. It's disgusting. I thought it was just murder, but they eat them."
Gabriela Rico Jiménez was 21 years old when she was filmed outside the Fiesta Inn hotel in Monterrey, Mexico, in August 2009, making distressed accusations about cannibalism among the elite. After that night, she was never seen publicly again.
After her public outburst, Monterrey's DIF Police (Family Development police) intervened and detained her. According to local reports and a caption on the archived news footage, the following occurred:
She was initially taken to jail following her arrest
She was subsequently transferred to a psychiatric center at the Buenos Aires colony
Reports indicate she was to remain there "indefinitely" until she received help and could be properly cared for
Crucially, no official update has been provided since 2013 regarding her condition or whereabouts. A person claiming to be a law student who encountered Jiménez at the facility where she was held after her arrest provided a first-hand account.
According to this witness:
They described her as being in a state of "despair, fear, anguish" and appearing "weary of the environment"
When approached, Jiménez allegedly told them "we were all dead, that we were all dead, that we were among them"
After approximately 20 minutes, "some tall, well-dressed people arrived" and removed the witness from the area
The witness claimed that when they later inquired with senior officers about her case, they were told: "Really, if she does not exist, she never existed, and you do not work here"
This account remains unverified, as the witness chose to remain anonymous. While her case has resurfaced following the January 2026 release of Epstein-related documents, no evidence has been found linking Gabriela Rico Jiménez to Jeffrey Epstein. However, it's still an interesting case in this context.
For researchers documenting RSA/SRA patterns, Epstein Island presents several elements consistent with documented case literature:
Isolated Geographic Setting: Island accessible only by boat or helicopter; consistent with "closed system" environments documented in SRA cases
Symbolic Architecture: Deliberate use of religious and occult symbolism (cube, dome, octagon, stripes, Poseidon) suggests ritual function
Inversion of Christian Imagery: Gold dome, blue/white stripes (Marian colors), papal portrait; then subverted by Poseidon, carnivorous birds, and anti-Christian statements
Medical Apparatus: Dentist chair and masks correspond to documented SRA patterns involving medical torture and "watching" imagery
Ritual Allegations: FBI files contain sworn testimony of sacrifice, cannibalism, and infant consumption; whether true or false, these allegations are now part of the official record
As with the Project Monarch material discussed earlier, the ritual abuse allegations in the Epstein files occupy a contested evidentiary space: The temple exists; the dentist chair and masks exist; the FBI interviewed a witness who made these statements; the DOJ released the files with a disclaimer. Whether the witness's statements are true; whether ritual sacrifice occurred on the island; whether infants were killed and consumed—this needs substantiation.
The DOJ's disclaimer explicitly warns that some materials may be "false or fraudulent." This does not mean the witness was lying; it means the information has not been corroborated and does not form the basis of criminal charges.
Within our analytical framework—that the same institutions conducting operations also control information—the DOJ's disclaimer could itself be interpreted as a mechanism for discrediting genuine allegations. That interpretive choice remains with the researchers.
Part VI: Global & Temporal Parallels
Wayward is not purely fiction. It draws directly on the real-world "troubled teen industry," a network of behavior modification programs, wilderness camps, and residential treatment facilities that have been documented to use abusive techniques similar to those depicted in the series.
As Mae Martin, the series creator, told reporters: "I was a wayward teen in the early 2000s, and my best friend was sent to one of these troubled teen institutes when she was 16. She came back and had just the craziest stories about it."
The real-world programs have been documented to use:
Isolation and sensory deprivation
Physical restraints and corporal punishment
Group confrontations similar to the "Hot Seat"
Solitary confinement ("the Mirror Room")
Forced drugging
Abuse that continues for years, often without oversight
The connection to SRA and RSA is not direct, but the methods are identical: Burrow, Break, Build, Ascend, Leap. The language is different, but the architecture is the same.
Epstein, Maxwell, and the Intelligence Connection
The Jeffrey Epstein case provides a contemporary parallel to the patterns documented in this paper. Epstein, like the abusers in SRA networks, had:
A network of powerful protectors
Filmed abuse used for blackmail
A multi-generational operation (recruiting victims who later recruited others)
Alleged intelligence connections (his father-in-law Robert Maxwell's documented links to Mossad; his own relationship with Ehud Barak)
The Epstein files, released in 2025 and 2026, have renewed attention to these connections. Whether Epstein was a "Mossad asset" or a predator with powerful friends, the pattern is consistent: abusers with elite connections are protected; their victims are disbelieved; the truth emerges only after they are dead.

Part VII: Legacy & Contemporary Relevance
The most important legacy of the SRA/RSA/MK-Ultra phenomenon is the survivor movement. Organizations like Survivorship and S.M.A.R.T. have created spaces where survivors can share their stories, find support, and advocate for recognition and justice.
These survivors face immense obstacles. They are often disbelieved. Their recovered memories are dismissed as false. Their trauma is minimized. Yet they continue to speak, to organize, to demand accountability.
Alison Miller's Demystifying Mind Control and Ritual Abuse: A Manual for Therapists represents a landmark in the therapeutic response to SRA and RSA. Miller, a clinical psychologist who has worked with survivors for decades, provides a framework for understanding the specific psychological structures created by programming and a protocol for helping survivors heal.
Miller's work is controversial. Mainstream psychology largely dismisses the reality of organized ritual abuse, but mainstream can rarely be trusted when it involves the elite (degenerate) class, many of whom own the institutions where they are employed. But for the survivors who have found their way to her, her framework has been life-saving.
The Wayward Effect: Fiction as Truth-Telling
Wayward represents a new kind of truth-telling. By framing the architecture of trauma-based mind control within a fictional narrative, the series has reached an audience that would never engage with survivor testimony or declassified CIA documents. It has made visible the invisible.
The series' success, becoming Netflix's No. 1 global show, suggests that there is an appetite for this truth. People want to know how these systems operate. They want to understand why they have been told these things never happened.
Despite decades of investigation, many questions remain:
What was the full scope of MK-Ultra? The destruction of records in 1973 means we may never know.
Did MK-Ultra techniques transfer to other programs? The continuity between government mind control research and SRA/RSA networks remains disputed.
How widespread is organized ritual abuse? Survivor testimony suggests it is more common than acknowledged, but corroborating evidence is often lacking.
What is the relationship between SRA, RSA, and intelligence agencies? The pattern of connections—Robert Maxwell, Ehud Barak, Jeffrey Epstein—suggests something, but proof remains elusive.
How do we distinguish real abuse from moral panic? The conflation of legitimate allegations with false memories has made this distinction nearly impossible.
While exploring these different illegal applications of 'mind control,' it is essential to recognize that the psychological mechanisms documented in this project—dissociation, trauma bonding, coercive control, and programmed obedience—are not exclusive to clandestine intelligence operations or ritual abuse networks.
They are the same strings that are pulled in millions of intimate relationships every day, often by abusers who have never heard of MK‑Ultra or Project Monarch. The difference is not one of kind but of scale and intentionality.
A husband who systematically isolates his wife, alternates cruelty with kindness, and punishes her for independent thought is using the same core levers as an organized cult that conditions child victims through ritualized trauma.
The husband may not label his behavior “mind control,” but the effect on the victim’s psychology—learned helplessness, fractured identity, inability to leave—is indistinguishable from the documented outcomes of deliberate programming.
At the other end of the spectrum, criminal networks and intelligence‑adjacent groups actively research and refine these mechanisms, applying them with cold precision to produce obedient operatives or blackmail assets. The underlying architecture of control is identical; only the context and the abuser’s self‑awareness differ.
Understanding this continuum allows us to see that the “domestic abuser’s playbook” is not a separate phenomenon; it is the foundational layer upon which larger systems of organized abuse are built.
Part VIII: The Domestic Abuser’s Playbook
The stages of trauma‑based mind control are not confined to secret government programs or hidden cults. They are the very blueprint that domestic abusers use, often unconsciously, to trap, break, and rebuild their partners.
The same architecture explains the paradox that has puzzled outsiders for generations: why victims of domestic violence frequently stay, defend their abusers, and sometimes even become complicit in the abuse of others.
Phase 1: The Grooming Stage
In the early days of a relationship, the abuser engages in what survivors and therapists call the “grooming” or “love‑bombing” phase. This is the stage where the abuser burrows into the victim’s life, becoming indispensable.

The abuser presents as attentive, romantic, and deeply understanding. They may mirror the victim’s interests, sweep them off their feet, and create a sense of a once‑in‑a‑lifetime connection.
Simultaneously, they begin isolating the victim from friends, family, and support systems; often under the guise of love (“They don’t understand us,” “I just want you all to myself”).
In Wayward, Evelyn Wade isolates her students by cutting off their contact with the outside world. A domestic abuser does the same, but more slowly. The victim gradually stops seeing friends, moves away from family, and becomes financially dependent. The abuser becomes their entire world; just as Evelyn becomes the world for the students of Tall Pines.
Phase 2: The Shattering of Self
Once the victim is sufficiently isolated, the abuser begins the abuse. This is where the psychological and often physical violence escalates.

The abuser uses intermittent reinforcement, alternating affection with cruelty, to create confusion and dependency. A victim may be subjected to screaming, hitting, gaslighting (“You’re crazy, that never happened”), financial control, and sexual coercion.
The unpredictability of the abuse keeps the victim in a constant state of hypervigilance, breaking down their ability to trust their own perceptions.
Neurobiologically, this phase exploits the same appeasement circuits described earlier. When faced with a threat that cannot be escaped, the nervous system shifts into a dissociative, compliant state. The victim learns that fighting back leads to worse punishment, while compliance may earn temporary peace.
Survivors often describe feeling like they are “losing themselves,” “going crazy,” or becoming a “shell.” This is the same ego dissolution that MK‑Ultra sought to achieve with drugs, and that SRA cults create through ritual terror.
Phase 3: Rebuilding in the Abuser’s Image
After the victim is broken, the abuser begins the Build phase. This is the “honeymoon” period that follows an explosion of abuse. The abuser apologizes, makes grand gestures, and promises change.

They may buy gifts, cry, or threaten self‑harm. The victim, starved for affection, clings to these moments as proof that the abuser loves them and that the relationship can work.
The abuser subtly (or overtly) dictates how the victim should behave: what to wear, who to speak to, how to act. The victim’s new identity is constructed around pleasing the abuser. They become hyper‑attuned to the abuser’s moods, walking on eggshells, and internalizing the abuser’s criticisms (“You’re worthless without me,” “No one else would put up with you”).
Psychologists call this trauma bonding. It is the same mechanism used in SRA and RSA: the abuser alternates terror with kindness, creating a powerful attachment based on the hope that the good times will last.
The victim begins to believe the abuser’s narrative; that they are flawed, that the abuse is their fault, that leaving is impossible.
Phase 4: Supervised Existence
In the Ascend phase, the victim functions in the outside world while remaining under the abuser’s control. They may go to work, raise children, and maintain a public facade of normalcy. But every decision is filtered through the abuser’s expectations.

The victim learns to present a version of the relationship to outsiders that conceals the abuse. They may even believe that the abuse is normal or that they deserve it. If they do try to speak out, they often find that friends, family, and authorities dismiss their concerns; especially if the abuser is charismatic, respected, or wealthy.
This is the same dynamic that survivors of SRA and RSA describe: living a double life, where the public self seems normal while the internal reality is one of control and terror. It is also the experience of the “graduates” of Tall Pines, who live in the town, appear healed, but remain under Evelyn’s system.
Phase 5: The Transformation into Abuser
The final, most tragic phase is when the victim becomes the abuser. In domestic abuse, this can take several forms.

Some victims, after years of being controlled, learn to use the same tactics on their children; perpetuating the cycle intergenerationally. Others, when they finally leave, may enter a new relationship and find themselves repeating the patterns they endured, either as abuser or as victim again.
In the Wayward series, Laura’s transformation into the new Evelyn is the ultimate metaphor for this cycle. She does not escape the system; she internalizes it. The victim becomes the new cult leader, replicating the trauma onto the next generation.
Domestic abuse research consistently finds that childhood exposure to violence is a primary predictor of later perpetration or victimization. The cycle of abuse is not a moral failing; it is the result of programming that began with the abuser’s own childhood.
The tragedy is that the system of control reproduces itself, turning the broken into breakers.
Why Victims Stay — The Cold Logic of Appeasement
When seen through the lens of the five‑phase model, the question “Why don’t they just leave?” becomes absurd. Leaving would mean:
Abandoning the only identity they have been allowed to have
Confronting the terror of the unknown after being broken
Losing the intermittent rewards they have been conditioned to crave
Risking escalation or death from an abuser who has promised to hunt them down
The victim’s nervous system has been rewired to treat the abuser as both threat and source of safety. The same appeasement circuits that kept them alive during the Break phase now compel them to stay.
Moreover, the 'supervise existence' phase teaches the victim that no one will believe them, or that they deserve what they receive. By the time they might consider leaving, they have often lost all financial resources, all social connections, and all sense of their own agency.
Parallels with SRA, RSA, and MK‑Ultra
The domestic abuse cycle is not categorically different from the other forms of trauma‑based mind control examined in this paper. It is simply the most common, the most normalized, and the most invisible.
Burrow | Love‑bombing, isolation, grooming | Recruitment, selection, birth into cult
Break | Escalating violence, gaslighting, intermittent terror | Ritual torture, LSD, electroshock, forced witnessing
Build | Trauma bonding, creation of dependency, internalization of blame | Programming of alters, illusion of love, forced perpetration
Ascend | Public facade, financial control, social isolation | “Sleeper” assets, double life, surveillance
Leap | Intergenerational cycle, victim becomes abuser | Victim becomes recruiter or cult leader
Implications for Intervention
Recognizing domestic abuse as a form of trauma‑based mind control shifts how we must respond. Traditional approaches like offering shelters, restraining orders, counseling are necessary but insufficient. They do not address the deep psychological conditioning that keeps victims trapped.
Effective intervention must:
Re‑establish a Burrow of safety: Remove the victim from the abuser’s sphere of influence completely, often through coordinated safety planning and long‑term relocation.
Support the rebuilding of self (a healthy Build): Provide trauma‑informed therapy (from a therapist who knows what they're doing and has the victim's best interests at heart) that helps the victim reconnect with their pre‑abuse identity and develop a new sense of self, not merely escape the old one.
Break the cycle of appeasement: Teach survivors to recognize the physiological and psychological responses that kept them compliant, and help them develop new, self‑protective responses.
Address the Leap: Work with survivors who may have harmed their children or others, understanding that this was part of the programming, and break the intergenerational transmission.
The five phases of Wayward are not just the architecture of a fictional cult; they are the hidden architecture of millions of abusive relationships. Domestic abuse survivors are not weak or irrational; they are victims of a systematic process of isolation, breaking, rebuilding, and control; the same process that was weaponized by the CIA, refined in SRA cults, and perfected in RSA networks.
Recognizing this does not excuse the harm that some survivors may go on to cause, but it demands that we see the cycle for what it is: a system of control that replicates itself across generations, destroying both the abused and the abuser. The only way to break the cycle is to understand it; and to intervene at every phase with the same cold‑logic precision that the abusers used to create it.
Part IX: From Intimate to Mass Control
The framework developed to understand domestic abuse—isolation, breaking, rebuilding, exploitation, and maintenance—operates not only in intimate relationships and organized abuse networks but also, when scaled, as a mechanism of mass control.
The premise here is straightforward: if psychological control works on an individual, it can work on a population when the same levers are pulled at scale. Social media, born from government-funded research and designed with behavioral conditioning baked into its architecture, provides the most powerful instrument for this mass application ever created.
The DARPA Pattern: Capture, Optimize, Deploy

The internet infrastructure that enables social media was not a private-sector invention that government later regulated; it was a government creation from the start. The Advanced Research Projects Agency (ARPA, later DARPA) of the U.S. Department of Defense developed ARPANET in the 1960s as a military resource-sharing network, driven by Cold War concerns that a Soviet attack on the phone system could cripple command centers.
By 1969, ARPA had connected the first computers at UCLA and Stanford, and by 1983, the adoption of TCP/IP protocols transformed this military network into the technical foundation of the modern internet.
The first message sent over this network came from a Pentagon-funded initiative. More directly, Google's foundational technology emerged from a 1995 DARPA grant—specifically a joint CIA/NSA program called the Massive Digital Data Services Program—that funded Larry Page and Sergei Brin's PhD work at Stanford.
Google Maps began as CIA satellite software that Google purchased. As Mike Benz, a former State Department official, testified, "Google itself started as a CIA/NSA project" and became a military contractor in 2004, its first year as a private company.
The architecture of global connectivity—the very infrastructure upon which Facebook, Google, and every other platform depends—was designed, funded, and initially operated by the defense establishment before being handed to the private sector for "commercialization."
The mechanism by which DARPA operates follows a consistent pattern: identify, extract, optimize, and redeploy through controlled channels. Nikola Tesla serves as the archetypal case. In the early 1900s, Tesla envisioned a global wireless communication and energy transmission system, constructing the Wardenclyffe Tower on Long Island with financing from J.P. Morgan.
When Morgan realized that Tesla's true vision was free, universal energy—a system that would bypass metering and corporate control—he withdrew funding, and Tesla was systematically marginalized, his patents seized or expired, his tower dismantled.
Approximately 120 years later, DARPA launched the POWER program (Persistent Optical Wireless Energy Relay) to develop a revolutionary wireless energy transfer system using lasers and drones, explicitly acknowledging Tesla's original vision as inspiration.
In 2025, DARPA successfully transmitted over 800 watts of power across 8.6 kilometers using a laser beam; Tesla's dream, now optimized for military logistics and forward operating bases. The inventor was ruined; the agency inherited and refined the concept.
DARPA's extraction mechanism operates through multiple channels. The agency uses flexible contracting tools called "Other Transactions" (OTs), which bypass traditional federal acquisition regulations, allowing DARPA to partner with "non-traditional defense contractors," including individual inventors, small startups, and academic researchers.
Through programs like DARPA Toolbox, the agency provides pre-negotiated access to intellectual property and commercial tools, effectively creating an ecosystem where innovations flow into DARPA's portfolio. Once a technology is proven, DARPA transfers it to other government agencies for "real implementation"—or, crucially, it seeds the technology into the private sector through friendly companies.
The LifeLog project (2003-2004) is the most direct predecessor to modern social media surveillance. LifeLog was a DARPA program designed to create a "near-perfect digital memory" tracking every phone call, email, television watched, newspaper read, airline ticket purchased, and more.
The explicit goal was to build a database capable of modeling human existence, inferring routines, relationships, and habits; training data for artificial intelligence and behavioral prediction.
When LifeLog was publicly exposed, Congress defunded it in 2004 due to privacy backlash. That same year, Facebook launched. According to investigative accounts, the CIA's venture capital arm In-Q-Tel provided seed funding for Facebook, and DARPA personnel moved directly into leadership roles at the company; most notably Regina Dugan, former DARPA director, who headed Facebook's "Building 8" division, where projects involving mind-reading technology and behavioral manipulation were developed.
The pattern is consistent: government develops surveillance infrastructure, public rejects it, technology is privatized through a "chosen plant" (Zuckerberg described by some as a "figurehead" rather than an independent founder), and the system is redeployed under commercial cover.
This is the DARPA playbook: identify a visionary concept (Tesla's wireless energy, Licklider's "Intergalactic Computer Network," LifeLog's total surveillance), fund its development through flexible contracting that attracts independent innovators, optimize it for military and intelligence applications, and when public resistance threatens, privatize it through a controlled entity that can operate without constitutional constraints like search-and-seizure protections.
The inventor is either co-opted or crushed; the infrastructure is captured; the technology is redeployed at scale, often with the same individuals rotating between DARPA, Google, Facebook, and the CIA. The network is not broken; it is simply wearing different clothes.
The Government Framework for Behavioral Monitoring & Control
Social media platforms, therefore, are not neutral spaces that governments attempt to influence from outside.
They are technological systems built on government-funded research, staffed by personnel with intelligence community backgrounds, and integrated into what Benz describes as the "Whole-of-Society" model; a four-part network of government agencies, private tech platforms, civil society organizations, and media/fact-checking entities that "all move completely in concert, very deliberately."
Phase 1: Isolation — Breaking the Individual from the Collective
The first phase of 'behavioral control' is isolation; severing the victim's connections to alternative sources of support, information, and identity. Social media achieves this at mass scale through mechanisms that are not bugs but features of its design.
Family as the First Target: Research from Duke University's Polarization Lab has documented that "the number one reason people are harassed online is for expressing political views, and often that harassment occurs within families."
Social media reduces complex human beings to single political positions or controversial statements, displayed without context or nuance. When family members see only the most extreme version of a relative's opinion online—stripped of tone, body language, and the complexity that emerges in face-to-face conversation—the relationship fractures.
Dr. Chris Bail of Duke notes that if you only interact with "Uncle Bob" through his most inflammatory posts, "that has the power to tarnish your relationship with him, regardless of family ties."
The Replacement of Physical Community: Before social media, community was place-based: neighbors, coworkers, fellow congregants. These physical communities provided multiple overlapping bonds; a person might disagree with a neighbor politically but still rely on them for a ride to the airport or help with an emergency.
Social media replaces these multi-dimensional relationships with single-axis ideological tribes. As one analysis puts it, social media has "reduced direct, face-to-face contact within society, institutions, and even within the family," accelerating a process of "social atomization" where individuals are "shut up in the solitude of his own heart."
Algorithmic Echo Chambers: The platforms do not passively reflect user preferences; they actively narrow them. Observers have noted that social media algorithms tend to show users more of the same type of content, even when users mark that content as "Not Interested," creating a sense that "something I don't want to see is being forcefully shown to me."
The effect is a curated reality where opposing perspectives are systematically filtered out, leaving the user isolated within an information ecosystem controlled by the platform.
Phase 2: Breaking — Systematic Degradation of Existing Identity
Once isolated from countervailing influences, the victim must be broken down; their existing beliefs, values, and sense of self systematically degraded. Social media accomplishes this through built-in mechanisms that induce shame, fear, and self-doubt.
The Popularity Contest: Social media transforms every human interaction into a quantified popularity contest. "It's engineered to scare and shame us; mainly by being a nonstop global gauge broadcasting our aloneness and unpopularity for all to see."
Every post receives a numerical score: likes, shares, retweets, comments. These metrics are public. The result is a system where "our skills seem worthless" compared to the manufactured success of others, where "self-confidence and self-compassion seem ridiculous compared to the opinions of three million strangers half a world away."
Performativity and Surveillance: The platform architecture compels users to perform for an unseen audience. "On virtual stages, we pose. Performativity turns every word we type and every picture we post into a recital, everyplace we are into a stage; and thus every reality less real."
Meanwhile, users are encouraged to "expose ourselves and love being surveilled," internalizing the very monitoring that would have seemed dystopian in any previous era.
Moral Outrage as Social Currency: Research from NYU's Center for Conflict and Cooperation has found that "receiving positive feedback on 'morally outraged' posts encourages people to express more moral outrage in the future."
People have "social incentives" to express outrage, which leads them to "exaggerate their expressions of outrage" and causes others to "overestimate how morally outraged others actually are."
The result is an outrage cycle that drives polarization, public shaming, and hate speech; all while the platform captures the engagement metrics. As the research notes, "moral-emotional rhetoric online is linked to the spread of misinformation, hostility, and the formation of echo chambers" and can "translate into real-world violence."
Shaming as a Control Mechanism: The domestic abuser shames the victim to destroy their self-worth. Social media systematizes this at scale. "All boundaries are broken," writes one psychologist. "Aspects of us that once would have stayed private, social media compels us to reveal—because it's edgy, might attract emojis, and we're among 'friends'."
The platform then weaponizes this exposure through the constant threat of negative feedback, public ridicule, and "cancellation"—the digital equivalent of the abuser's silent treatment or public humiliation.
Phase 3: Rebuilding — Inculcation of a New Identity
The broken victim is receptive to a new identity; one provided by the abuser. In the domestic context, this is the "honeymoon phase" where the abuser defines what the victim should believe, value, and prioritize. In the mass control context, social media platforms become the vehicle for inculcating new belief systems aligned with institutional interests.
Signaling Through Moral Language: Research demonstrates that "people who shared moral-emotional messages were perceived as strongly identified with their ingroup." Expressing moral outrage serves a social function: it signals belonging.
For individuals who "highly identified with their political party," the use of moral-emotional language caused them to share political content approximately 80% of the time.
The platform thus becomes an identity-reinforcement engine, where the user's sense of self is increasingly defined by the moral-emotional content they share and the ingroup whose approval they seek.
Building New Tribes: As old bonds (family, neighborhood, workplace) weaken, social media offers new ones: ideological tribes organized around shared grievances, enemies, and moral certainties. These tribes provide the belonging that humans require, but on terms dictated by the platform's engagement algorithms.
The more extreme the content, the more engagement it generates; the more engagement, the more the algorithm promotes it; the more it is promoted, the more it defines the tribe's identity. This is not organic community formation; it is engineered group identification.
The Whole-of-Society Consensus: The beliefs being inculcated are not random. Congressional testimony has documented that the Department of Homeland Security's CISA (Cybersecurity and Information Security Agency), in partnership with NGOs and tech platforms, actively worked to identify and suppress "heterodox" viewpoints during the 2020 election and COVID-19 pandemic.
Michael Shellenberger testified that this "Censorship Industrial Complex" used "sophisticated psychological operations and disinformation tactics developed abroad against the American people." The newly rebuilt identity, in this context, is one that aligns with the consensus produced by the government-platform-civil society-media network.
Phase 4: Exploitation — Using the Rebuilt Subject for External Ends
In the 'mind control' mechanism, the rebuilt victim serves the abuser's needs: providing domestic labor, financial support, political servitude, or sexual access. In the mass control framework, the rebuilt subject serves external interests; voting patterns, consumer behavior, support for military interventions, acceptance of policies that benefit the financial and military-industrial complex.
Political Exploitation: The 1996 U.S. presidential election saw the first use of internet platforms for political campaigning, with both Bill Clinton and Bob Dole utilizing online tools. What was novel then is now infrastructure. Social media platforms are the primary terrain of political battle precisely because they shape what voters believe, who they trust, and what they consider acceptable.
The platforms' ability to "throttle" certain content, as documented in the EIP (Election Integrity Partnership) reports, means they can influence election outcomes not through direct censorship but through algorithmic suppression. The EIP reported a 75% response rate from platforms and that 35% of URLs they flagged were "removed, labeled, throttled, or soft-blocked."
Consumer Exploitation: The attention economy is the economic engine of social media, but the exploitation goes deeper than advertising revenue. By shaping desires, fears, and aspirations, social media platforms direct consumer behavior in ways that benefit the financial interests of their shareholders and their government partners.
The user who has been broken down and rebuilt as an anxious, status-seeking consumer is optimally positioned to be exploited by the consumption-based economy.
Psychological Warfare Turned Domestic: Benz's testimony documented that "US and UK military contractors" deployed "sophisticated psychological operations and disinformation tactics" that had been developed for use in conflict zones; against the American people during the 2020 election.
The same techniques used to destabilize foreign governments and manage foreign populations (the "Whole-of-Society" counter-insurgency model) were repurposed for domestic information control. The target was no longer an enemy population; it was the citizenry of the United States.
Phase 5: Maintenance — Ensuring Continued Control
The final phase of the abuser's playbook is maintenance: keeping the victim in the controlled state indefinitely. Social media accomplishes this through addiction-based design and continuous feedback loops.
The Addiction Loop: Social media is designed to be impossible to quit. Notifications, infinite scroll, variable reward schedules (the same psychology as slot machines), and the fear of missing out (FOMO) keep users returning.
The result is that "we suffer, but can't quit, fearing that departing social media would cut us off from family, friends, society, and reality; and define us as failures or non-persons or freaks." The victim is trapped by the very system that broke them.
Continuous Reinforcement: The outrage cycle documented by NYU researchers does not have a natural endpoint. Each cycle of moral outrage leads to more moral outrage; each round of public shaming sets the stage for the next.
The platform's algorithms are optimized for engagement, and engagement is maximized by maintaining the user in a state of low-grade anxiety, moral certainty, and tribal hostility. Peace, nuance, and reconciliation are bad for metrics.
Surveillance as Deterrence: Users who might defect from the controlled state are deterred by the knowledge that their deviation will be public. Every like, share, and comment is recorded and visible.
In the domestic abuse context, the victim fears what will happen if they try to leave. In the mass control context, the user fears social death: cancellation, ostracism, public shaming by their own tribe. The platform's transparency, the very feature celebrated as democratizing, becomes the mechanism of control.
The Five Phases Applied to Mass Control:
Isolation | Severing contact with family and friends | Algorithmic echo chambers; harassment of family members online; replacement of physical community with ideological tribes
Breaking | Degradation, shaming, destruction of self-worth | Public popularity metrics; performative surveillance; moral outrage feedback loops; fear of "cancellation"
Rebuilding | Providing new identity that serves abuser | Ingroup signaling through moral-emotional language; Whole-of-Society consensus formation; adoption of platform-aligned beliefs
Exploitation | Using victim for abuser's ends | Political manipulation; consumer behavior direction; support for institutional interests (military, financial, policy)
Maintenance | Ensuring victim cannot leave | Addiction-based design; continuous outrage reinforcement; surveillance as deterrence; fear of social death
The framework presented here does not claim that every social media user is a victim of mind control in the same sense as survivors of organized abuse networks. Rather, it demonstrates that the same psychological mechanisms operate at different scales and with different degrees of intentionality.
At one end of the spectrum, a teenager who internalizes shame from seeing curated perfect lives on Instagram is experiencing the same "breaking" mechanism that an abuser uses to destroy a victim's self-worth; just without the abuser's conscious intent.
At the other end, government contractors who deploy psychological operations developed for foreign counter-insurgency against domestic populations, using platforms built on DARPA-funded infrastructure and staffed by intelligence community alumni, are engaging in mass control with deliberate, calculated intent.
The domestic abuser may not know they are using "mind control techniques." The social media engineer optimizing for engagement metrics may not think of themselves as designing a control system. The government official requesting content moderation may believe they are simply fighting misinformation. But the pattern, across scales, is the same. And as with the seven patterns documented earlier, the convergence of mechanisms—isolation, breaking, rebuilding, exploitation, maintenance—across domains suggests something more than coincidence.
The question, as with Epstein's island, is not whether the system exists. The question is what we choose to see when we look at it.
Part X: Conclusion — The Door That Remains Open
Wayward ends not with resolution but with a question. Alex has discovered the truth about Tall Pines. Laura has become the new Evelyn. Abbie has escaped, driving alone through the night, but what she is escaping to remains unknown.
The series leaves its audience with the uncomfortable realization that some doors, once opened, cannot be closed; and that the truth, once glimpsed, does not always set you free.
This is the lesson of the SRA/RSA/MK-Ultra phenomenon. The evidence does not resolve into a single, clean narrative. There is no simple ending in which the villains are defeated and the survivors live happily ever after. What exists is a tangle of truths, each supported by its own evidence, each contested by its own skeptics.
The Four Truths
The evidence on trauma-based mind control resolves into four distinct truths, each supported by its own evidence, each existing in tension with the others:
Truth One: Government mind control programs existed. MK-Ultra was real. The CIA spent millions of dollars trying to develop techniques to control human minds. They used LSD, electroshock, torture, and sensory deprivation. They experimented on unwitting subjects. They destroyed the evidence.
Truth Two: A moral panic occurred. In the 1980s and 1990s, therapists using discredited techniques "recovered" memories of Satanic ritual abuse from thousands of patients. These memories led to criminal prosecutions, destroyed families, and created a cultural panic. The vast majority of these allegations were false; but they also served the purpose of conflating and discrediting real child-related crimes, often by intelligence-linked networks.
Truth Three: Organized abuse networks exist. Religious cults, non-profit organizations, orphanages, charities, Jeffrey Epstein. Their cases are evidence of a pattern of organized abuse protected by institutions for decades. Many of these networks incorporate ritualistic elements, whether Satanic or otherwise.
Truth Four: The foreign scapegoat narrative is itself a cover. The story that the United States learned mind control techniques from Nazi and Japanese scientists, that the CIA was corrupted by foreign monsters, is a strategic misdirection. The chronology doesn't match: the CIA's interest in psychological warfare predates large-scale recruitment of German and Japanese personnel. The methodology was already domestic: LSD, electroshock, sensory deprivation were not secret Nazi inventions but extensions of American psychology and psychiatry operating on vulnerable American populations.
The recruitment of the so-called war criminals served a different purpose: it provided a ready-made scapegoat. When the programs were exposed, the blame could be placed on "those Nazi doctors" and "those Japanese vivisectionists," never on the American institutions that funded, staffed, and directed the experiments.
The CIA didn't need to import monsters. The monsters were already homegrown. But by pointing the finger outward, they ensured that the real source of the methodology—the military-industrial-academic complex, the deep American tradition of using vulnerable populations (prisoners, mental patients, orphaned children) as experimental subjects—remained in the shadows.
The Conflation Strategy
The key to understanding the SRA/RSA phenomenon is to recognize that these four truths have been deliberately conflated; and that the fourth truth explains why the conflation works.
The existence of government mind control programs and organized abuse networks was used to lend credibility to the moral panic. The moral panic, in turn, was used to discredit legitimate investigations into government programs and organized abuse.
The foreign scapegoat narrative was used to absolve American institutions of responsibility for techniques they had developed independently. The result is a fog of confusion in which nothing can be proven and everything can be dismissed.
This conflation serves the interests of those who conducted the programs and protected the abusers. As long as the truth remains confused—as long as the public argues about whether "Satanic panic" was real or fake, about whether Epstein killed himself or was murdered, about whether MK-Ultra succeeded or failed—accountability remains impossible.
The four truths are not contradictions. They are layers. Peel back the moral panic and you find real abuse. Peel back the real abuse and you find institutional protection. Peel back institutional protection and you find government programs. Peel back government programs and you find... American institutions, American scientists, American subjects. No Nazis required. No Japanese war criminals necessary. The capacity for systematic, organized trauma-based control was never imported. It was always here.
A Path Forward
If the pattern of conflation and obfuscation is to be broken, several steps are necessary:
Full declassification: The remaining classified documents related to MK-Ultra and other mind control programs must be released. The destruction of records in 1973 should be investigated as a crime; not as a bureaucratic oversight but as a deliberate act of evidence suppression.
Independent investigation: A truth commission with subpoena power should investigate the links between government programs and organized abuse networks. This commission must be independent of the intelligence community. It must also investigate the foreign scapegoat narrative as a potential cover story, not as settled fact.
Therapeutic reform: The mental health profession must develop protocols for working with trauma that do not rely on recovered memory techniques that have been discredited; while also not dismissing the reality of organized abuse. Both errors, credulity and dismissal, have served the abusers.
Institutional accountability: The institutions that have protected abusers must be held accountable. This includes accountability for the narrative strategies that have shielded them from scrutiny.
Acknowledgment of the conflation: Finally, the public must acknowledge that the SRA/RSA phenomenon contains interlocking truths. To dismiss all allegations as moral panic is to serve the interests of the abusers. To accept all allegations as literally true is to ignore the documented reality of false memory. To accept the foreign scapegoat narrative uncritically is to let American institutions off the hook for crimes they committed with their own hands. The truth lies in the space where government programs, organized abuse, moral panic, and strategic misdirection intersect.
A Final Reflection
In Wayward, Evelyn Wade often speaks of "the door in the mouth"—a metaphor for the secrets we swallow, the truths we cannot speak, the traumas we carry in our bodies.
The phrase is deliberately enigmatic, but its meaning becomes clear over the course of the series: the door is the threshold between the self we show the world and the self we hide. To open the door is to confront the truth. To keep it closed is to remain trapped in the patterns of the past.
The survivors of trauma-based mind control have been opening that door for decades. Their testimonies are consistent, their suffering is real, and their pursuit of justice is relentless. They have been dismissed as liars, as delusional, as victims of therapeutic suggestion, as pawns of a moral panic. But they keep speaking. They keep opening the door.
Wayward is not a documentary. It is not an exposé. It is a work of fiction; a thriller, a horror story, a meditation on adolescence and trauma. But it is also something more: a map of a terrain that has been deliberately obscured, a narrative that makes visible what institutions have worked to hide.
The door in the mouth is open. What comes out is not always coherent, not always verifiable, not always comfortable. But it is, at its core, a truth that demands to be heard.
And here is the truth that Wayward—perhaps unintentionally, perhaps deliberately—reveals: the monster was never foreign. The monster was not imported from Nazi Germany or Imperial Japan. The monster was not a Satanic cult that emerged from nowhere. The monster was built in government recognized public and private institutions, by human hands, on vulnerable people; often with intelligence agencies (CIA/Mossad) involved. The capacity for systematic, organized trauma-based control was never imported. It was always present.
The scapegoat narrative is not a footnote to the history of trauma-based mind control. It is an aspect of it applied to the public itself: the final stage of programming where the victim is made to believe that the evil came from outside, that the abuser was a foreign monster, that the institutions that conducted the experiments are innocent; just corrupted, just momentarily misled, just victims themselves.
That is the lie. And like all lies in a programmed system, it serves to keep the door closed.
And there is a second layer to that programming; one that activates precisely when people begin to see through the first.
When individuals start demanding accountability, real accountability, the system does not always respond with silence. Sometimes it responds with division.
It manufactures or amplifies events that fracture unity:
A supposed left-wing attacker targeting the right
A supposed right-wing extremist targeting minorities
A Muslim desecrating a Christian site
A Christian burning a Muslim text
An attack framed to inflame tensions around LGBT or trans communities
Whether real, manipulated, or opportunistically weaponized, the effect is the same: horizontal warfare. People are turned against each other. Victims are turned against other victims. Anger that should move upward (vertical accountability) is redirected sideways (horizontal conflict).
Instead of a unified demand for truth and justice, society fractures into tribes; each fighting the other, each convinced the other is the enemy. This is not random. It is structurally consistent with every control system described in this work.
Because a divided population cannot hold power accountable. A population locked in horizontal conflict cannot organize vertically. A population that sees enemies everywhere will never look up to see who benefits.
So the final threshold—the last door—is not just recognizing the system. It is refusing to be turned against each other once you do. To demand accountability without being redirected. To resist narratives that convert outrage into tribal hatred. To recognize when conflict is being used to dissolve unity.
Because once the victims begin fighting each other, the system no longer needs to hide.
It has already won.

Bibliography
Mainstream Sources:
Kinzer, Stephen. Poisoner in Chief: Sidney Gottlieb and the CIA Search for Mind Control. (MK-Ultra documentation)
Ofshe, Richard and Watters, Ethan. Making Monsters: False Memories, Psychotherapy, and Sexual Hysteria. (Moral panic analysis)
Pendergrast, Mark. Victims of Memory: Sex Abuse Accusations and Shattered Lives. (Critical of recovered memory therapy)
Survivor and Therapeutic Sources:
Miller, Alison. Demystifying Mind Control and Ritual Abuse: A Manual for Therapists. Karnac Books, 2024
Svali. "MK ULTRA/Assassin Programming." Suite101, 2001. (Survivor testimony)
Springmeier, Fritz and Wheeler, Cisco. The Illuminati Formula. (Detailed programming descriptions)
Scientific Sources:
Cantor, C. and Price, J. "Appeasement: A survival strategy." 2007.
Porges, Stephen. Polyvagal Theory. (Neurobiology of threat response)
European Journal of Psychotraumatology. "Appeasement: replacing Stockholm syndrome as a definition of a survival strategy." 2023
On Wayward:
Netflix Tudum: Official series coverage
The Viewer's Perspective: Full recap and ending explained
Azat TV: Series analysis
Classification: Investigative Analysis / Systemic Diagnostics
Methodology: Cold logic, pattern recognition, integration of mainstream and alternative sources with critical evaluation, narrative mapping using Wayward as framework

.png)



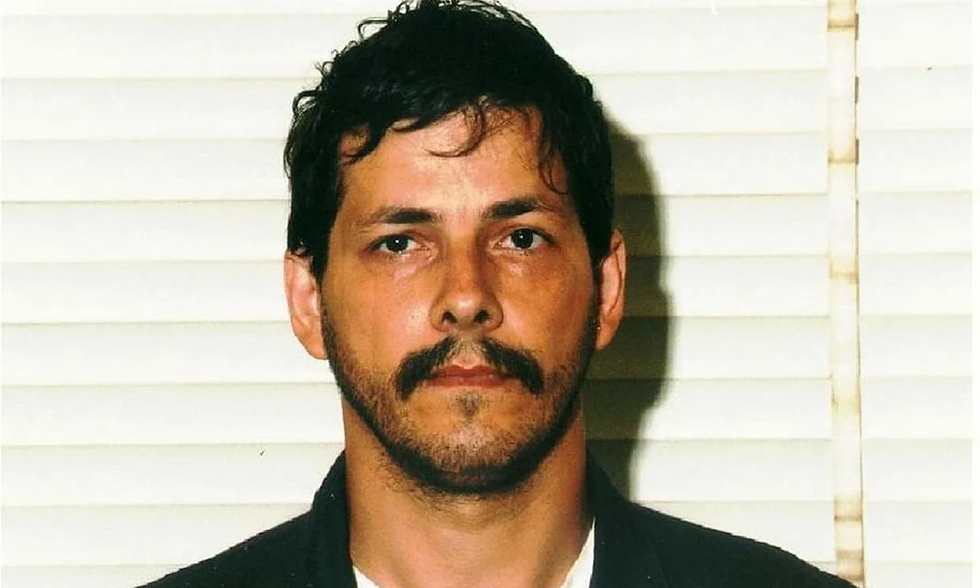
Comments